In my last few blog posts I have explained what is Azure information protection and how we can use it to protect sensitive data in an organization. You can access those using following links,
Step-by-Step Guide: Protect confidential data using Azure information protection
Step-by-Step Guide: Automatic Data Classification via Azure Information Protection
Step-by-Step Guide: On-premise Data Protection via Azure Information Protection Scanner
In this blog post I am going to demonstrate how we can use Azure information protection to secure sensitive data transfers over email.
My organization is using Office 365. With recent content search I found out sales team shares credit card details of customers via emails. These are very sensitive data and I want to make sure they can’t share these data with anyone else (internal or external).
To do that first I am going to setup a new label in Azure Information Protection. In my previous blog post http://www.rebeladmin.com/2018/12/step-step-guide-protect-confidential-data-using-azure-information-protection/ I explained how to setup labels so I am not going to repeat the steps.
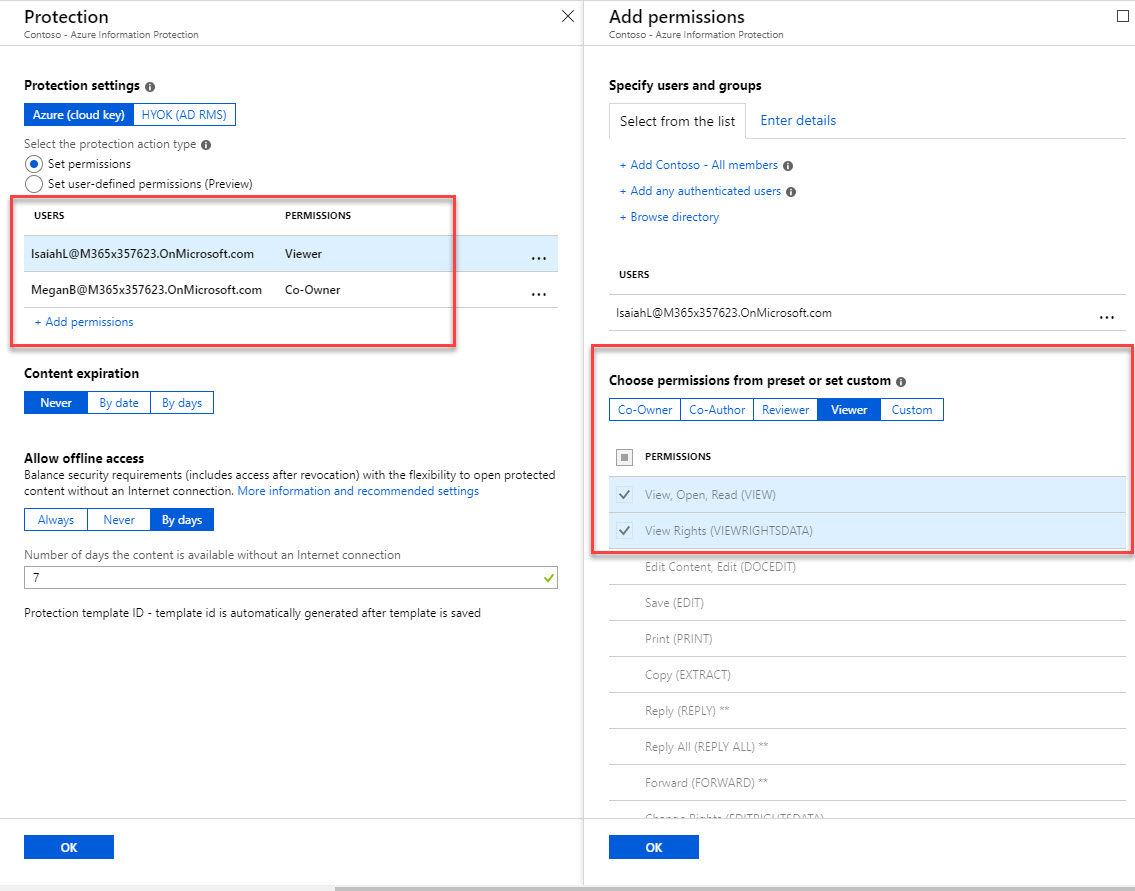
This new label is called CreditCardData. Megan is sales manager and she has co-owner permissions for the data with this label. Rest of the sales team is only having viewer permissions. They only can read the data. For testing purpose, I am using one of the sales user Isaiah.
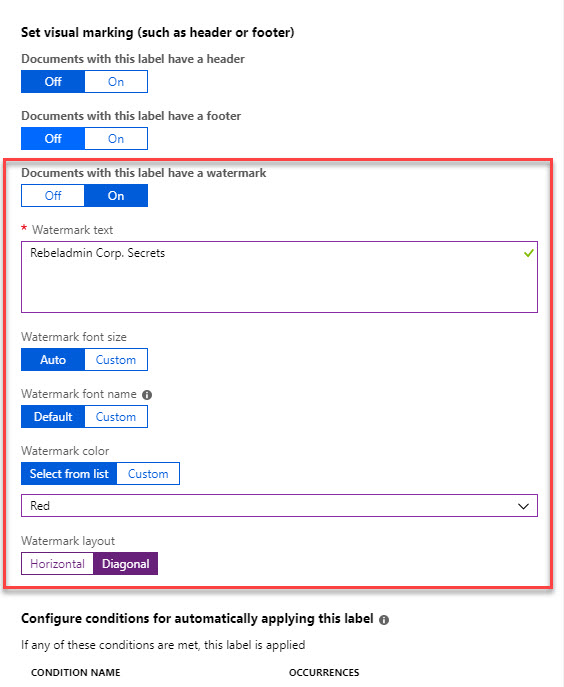
The data protected by this label will have watermark applied.
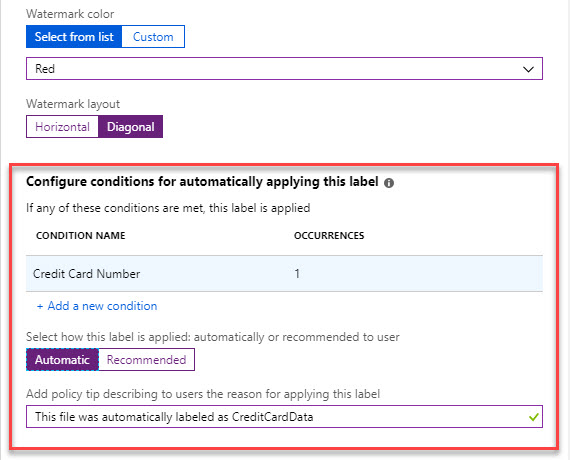
Also, I like to apply this label automatically to any data with credit card number. for that I am using a condition.
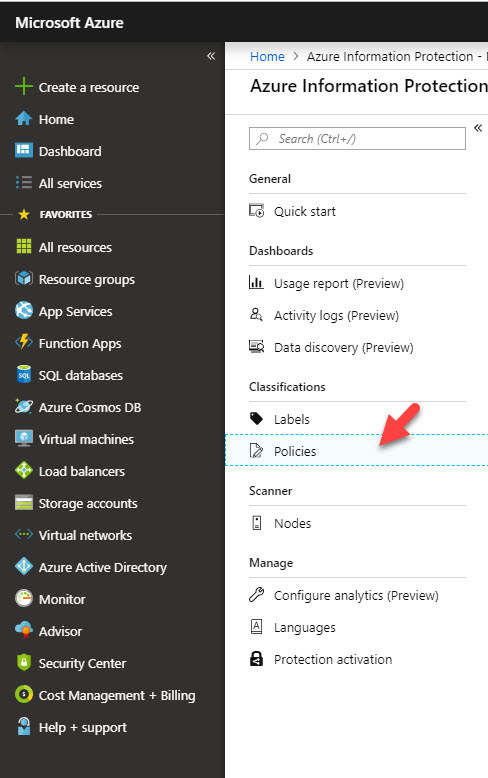
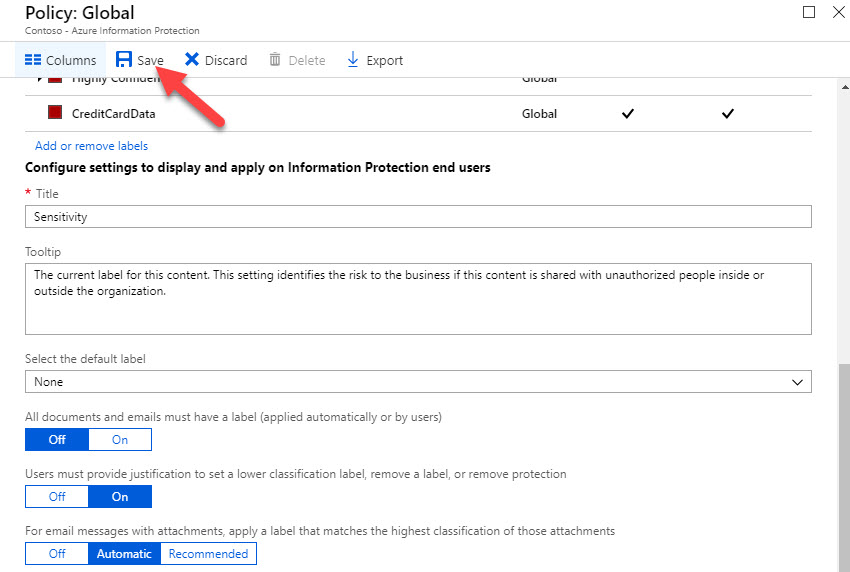
Now we have the label, next thing is to publish it. to do that,
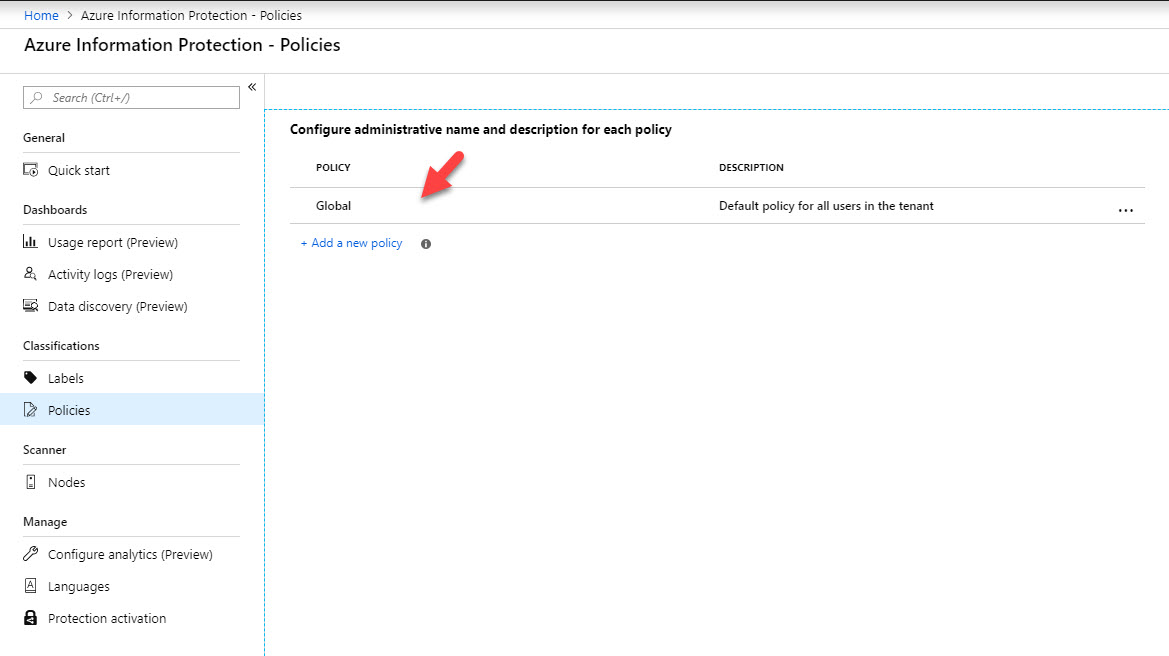
1) Go to Azure Portal | Azure Information Protection | Policies
2) Then click on Global Policy to edit it. It is possible to publish this new label under new policy too. but in my demo, I am going to publish it under global policy.
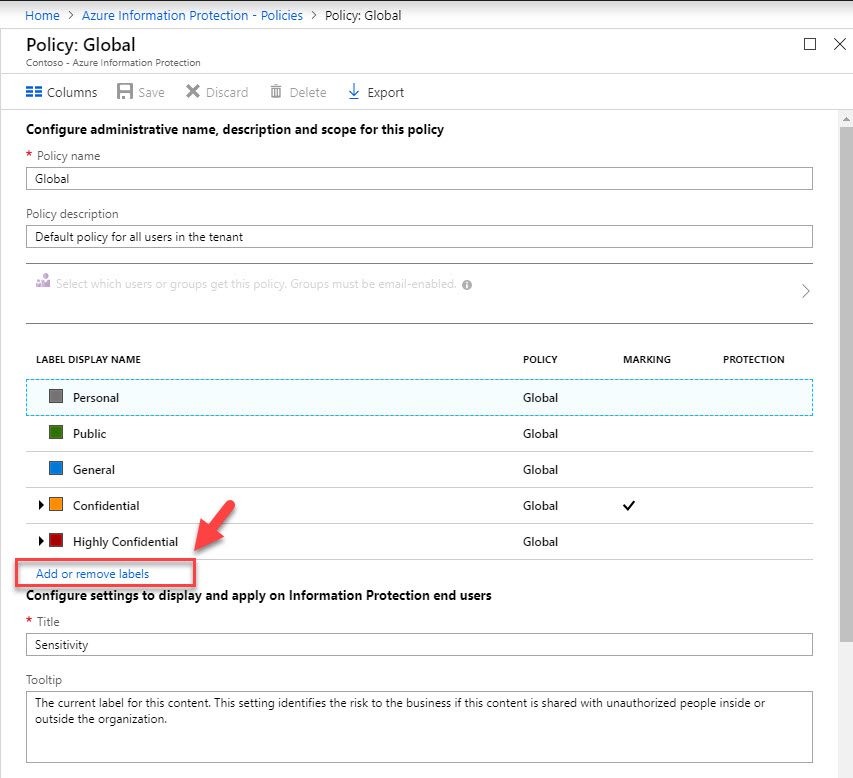
3) In new window, click on Add or remove labels.
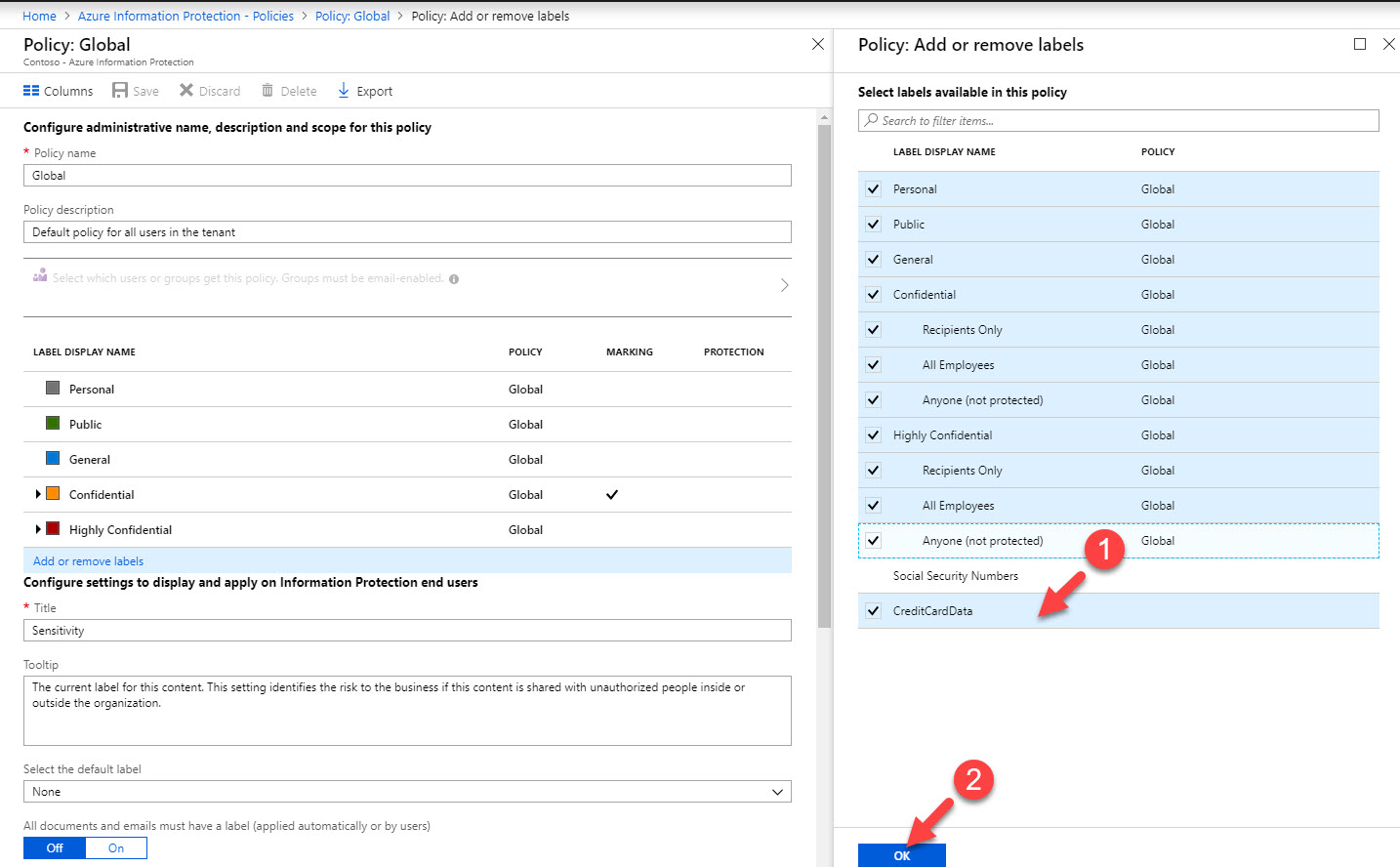
4) From the list, select new label we just created and click Ok.
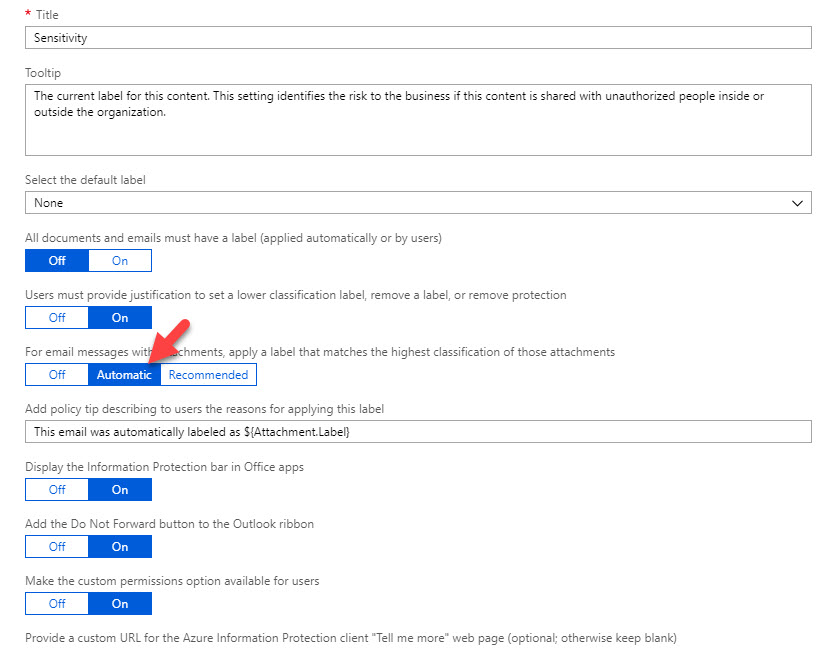
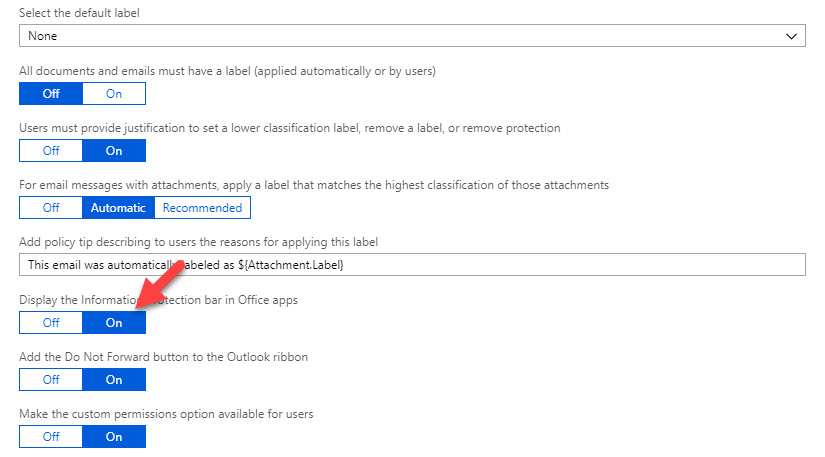
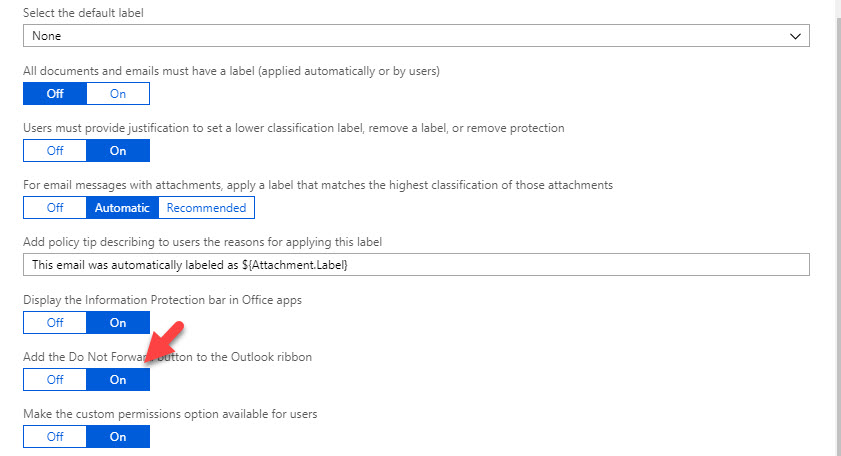
5) Then under option, For email messages with attachments, apply a label that matches the highest classification of those attachments select option Automatic.
6) For option, Display the information protection bar in office apps select On. This will enable protection bar in all office apps.
7) Also, click On for Add the Do Not Forward button to the outlook ribbon. According to new label setting, sales team members except Megan will not be able to forward email if it’s been tagged. But in future if we have users with more privileges, we can use this Do not forward option to make sure they can’t forward sensitive emails (based on label settings)
8) At last, click on Save to apply the settings.
This completes the configuration, lets do some testing,
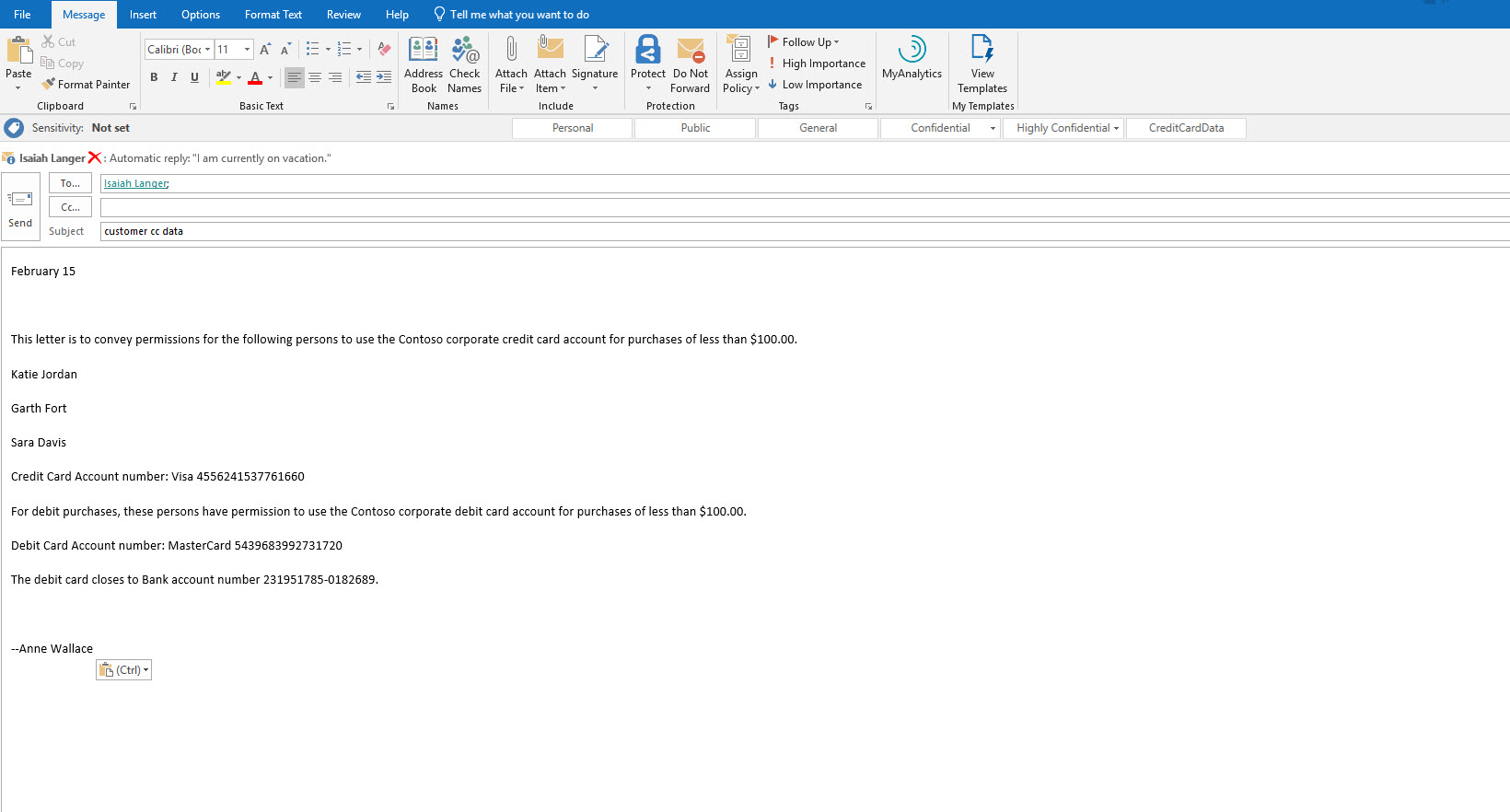
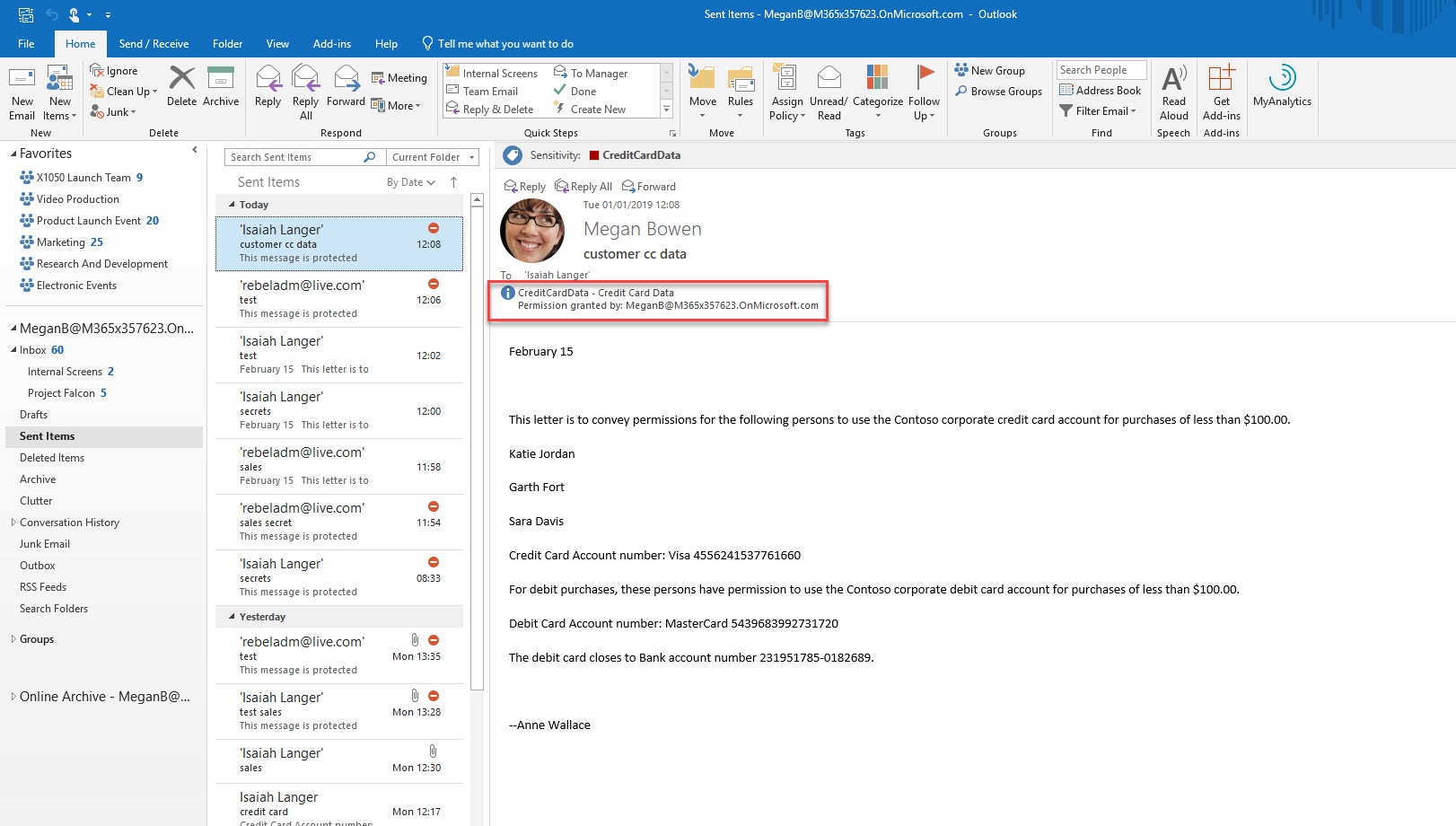
User Megan (Co-owner permissions) is sending an email with credit card data to Isaiah (Viewer permissions). she did not apply any classification to it before sending.
When I check sent items, i can see it got correct label automatically.
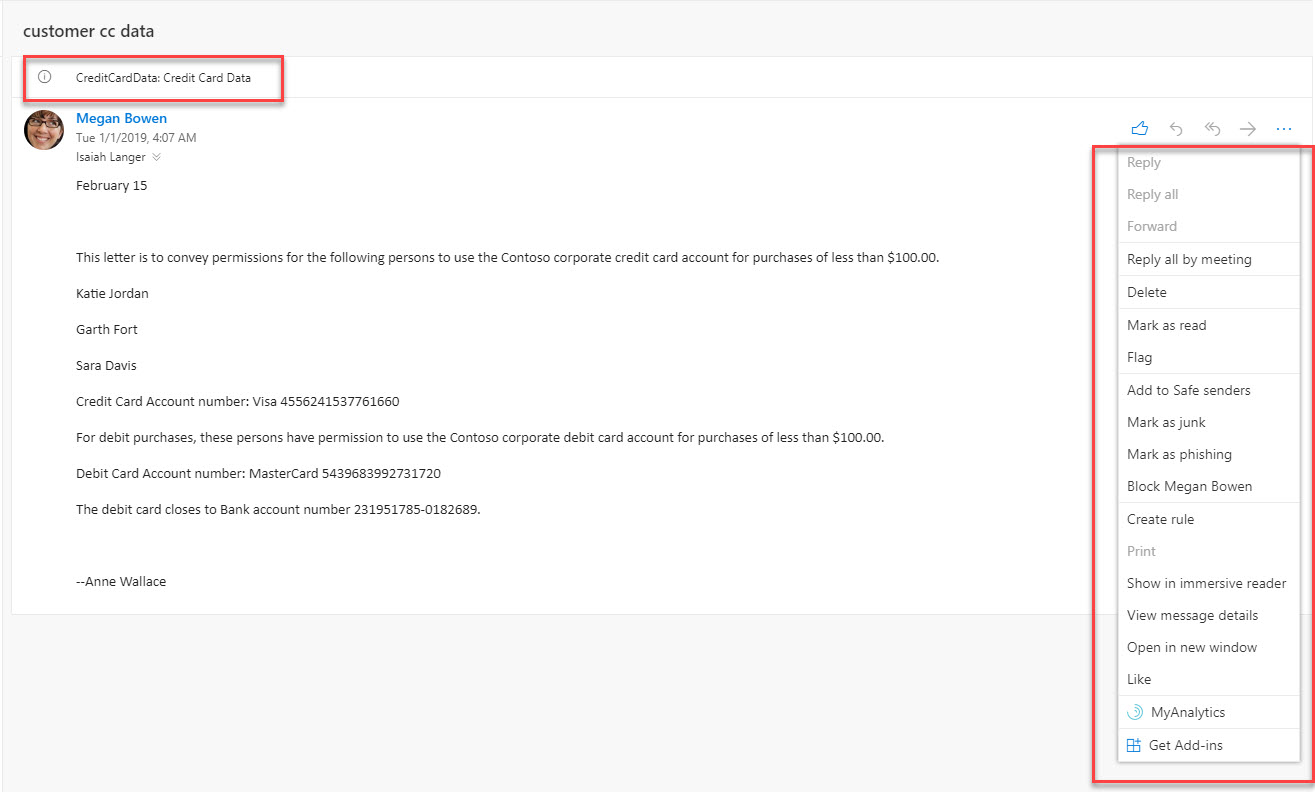
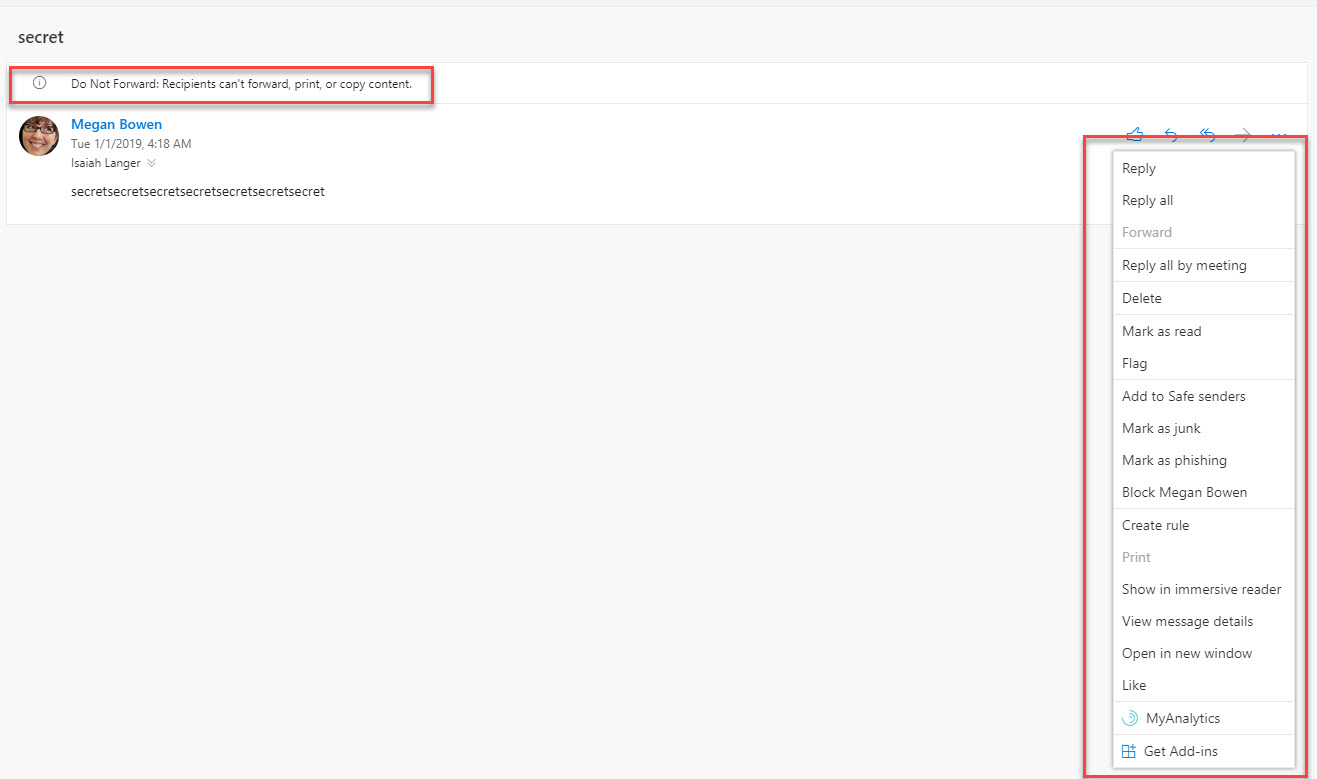
When I check Isaiah’s mail box using office app, I can see it also got correct label. Also, as expected he only can view the email, all other features such as forward, print is not available.
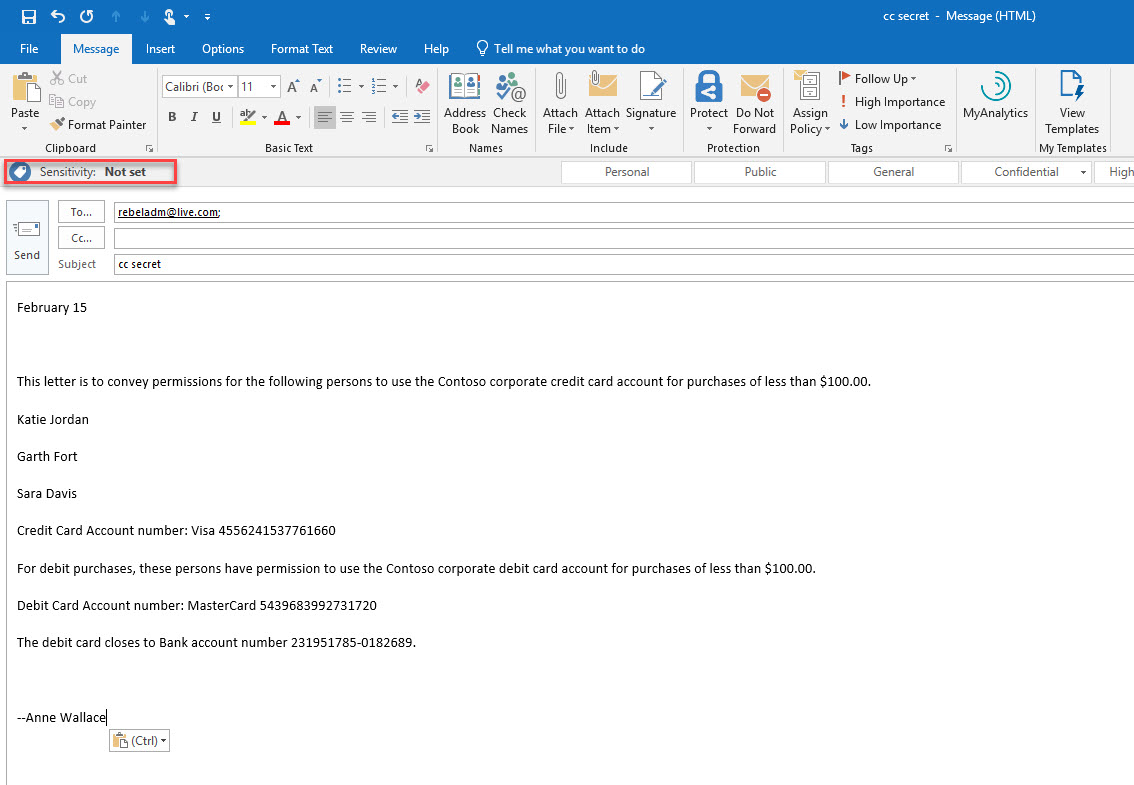
So, what happen if someone in sales send a new email to external contact with credit card details?
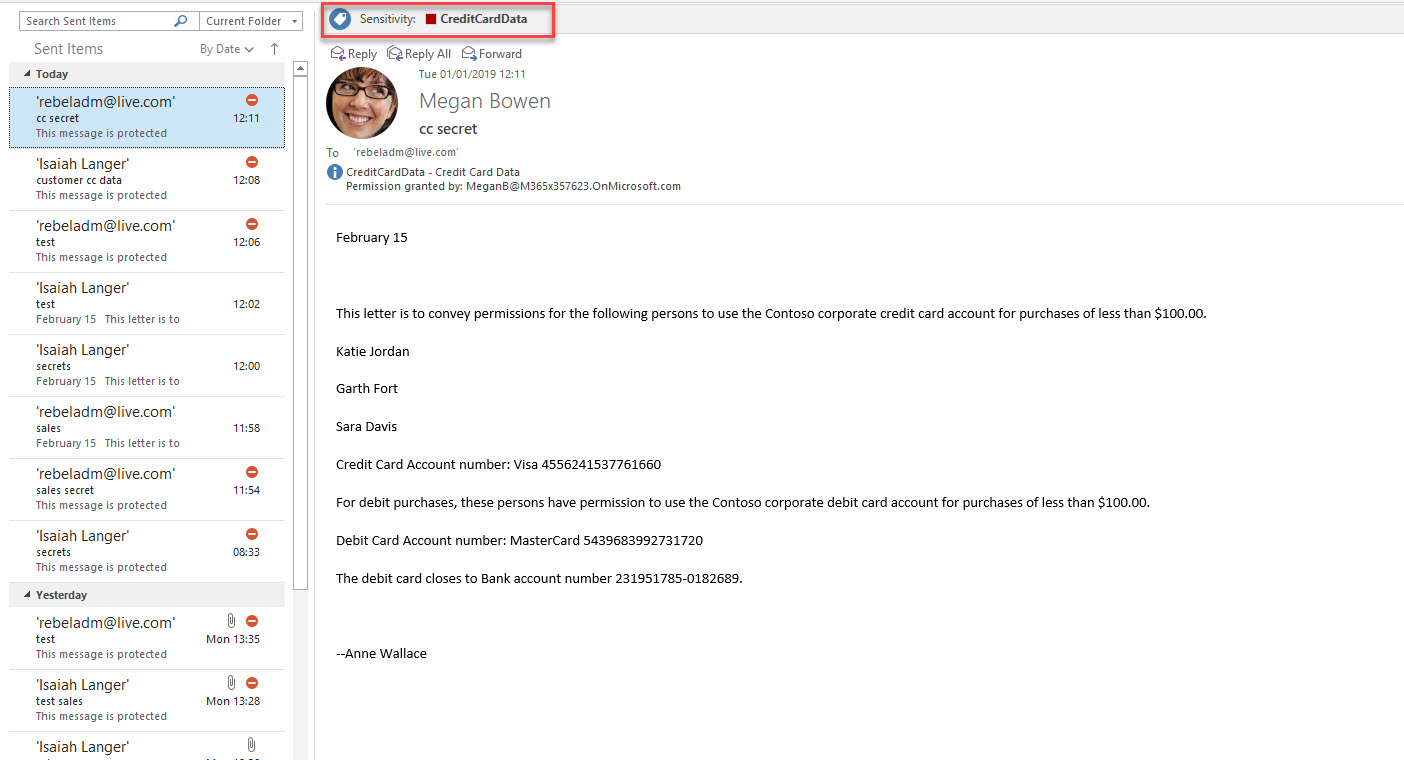
For testing I am sending an email with credit card details to rebeladm@live.com from Megan’s mail box. No label is set before send it out.
When I check sent box, I can see policy applied correct label to the email.
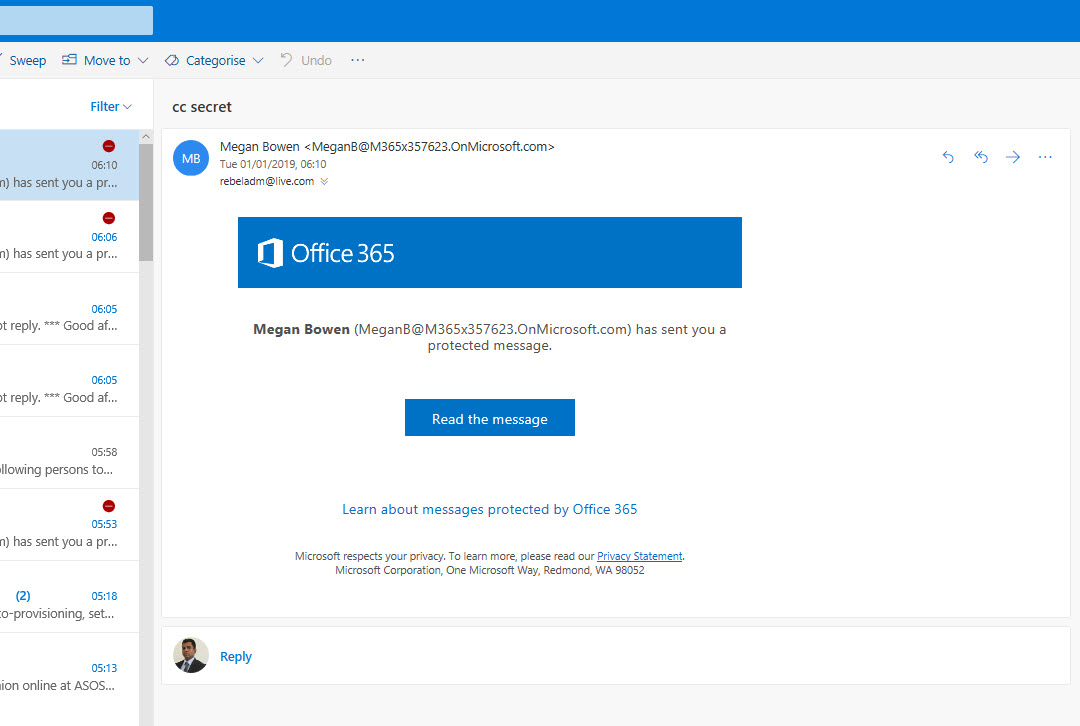
In receiver’s email box, he can’t view the content as expected. (if he clicks on read, he has to authenticate)
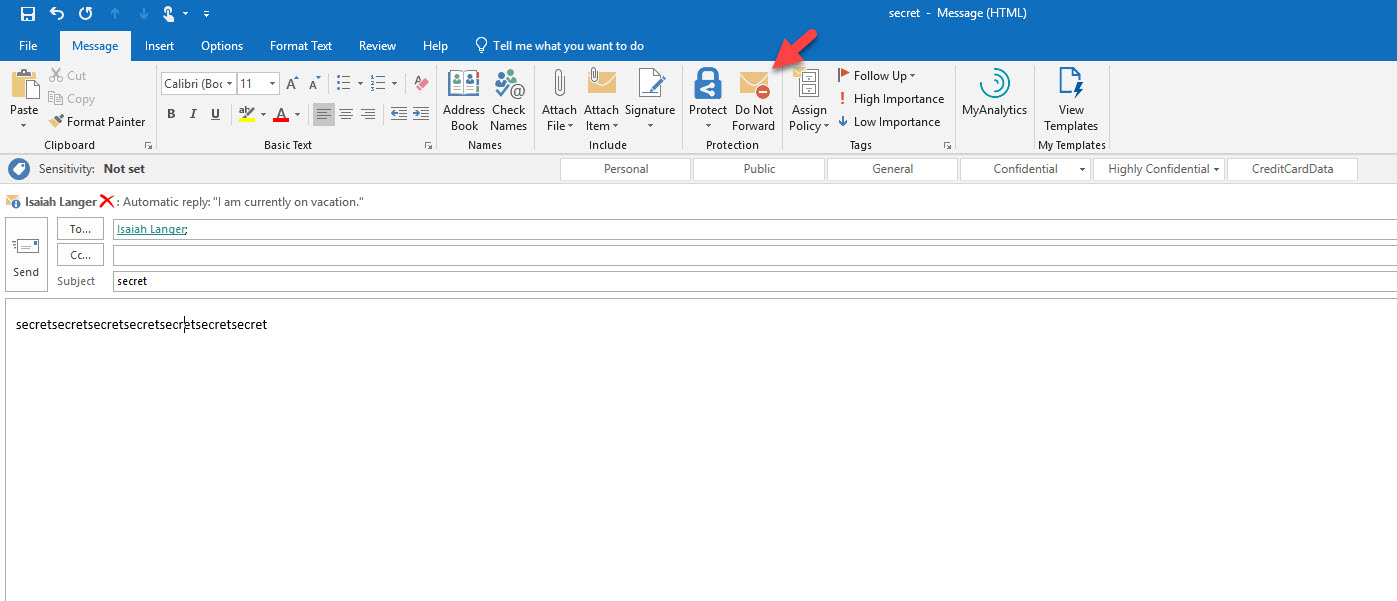
Also, let’s see if Do not forward option is working. In my test Megan is sending an email to Isaiah. This doesn’t have any credit card data. but she wants to make sure Isaiah can’t forward it.
So, before she sends the email she clicks on Do not forward button in the ribbon.
As expected when Isaiah receives the email he does not have forward or print option.
Cool ha? With a simple policy we can make sure users can’t share sensitive data using emails. This marks the end of blog post. If you have any further questions feel free to contact me on rebeladm@live.com also follow me on twitter @rebeladm to get updates about new blog posts.