In my last few blog posts I have talked about Azure AD conditional access policies and how we can use it to control access. In a conditional access policy, we define who have access to what applications from where. This is purely control the access to your app. Azure cloud app security allow us to extend these capabilities further into session level. using cloud app security, we can examine each session to the app in real time basis protect information further. Using cloud app security, we can create policies to,
1. Block downloads – Can define policies to block download of sensitive data.
2. Protect on downloads – instead of blocking download, we can create policies to allow users to download encrypted document after authentication, even though they are login from unmanaged device.
3. Monitor risky sessions – we can setup policies to monitor session of risky sign in. all the action from those sessions will be logged for further review.
4. Block access – If needed we can completely block access to apps if it’s from unmanaged device or non-corporate network.
5. Create read-only mode – we can create policies to create read-only mode for apps (for group of users)
More about cloud app security is available at https://docs.microsoft.com/en-us/cloud-app-security/what-is-cloud-app-security
In this demo, I am going to demonstrate how to integrate an app with cloud app security and then how we can create policies to control download of sensitive data. In this demo I am going to use salesforce application with CAS and block PDF file downloads. To start,
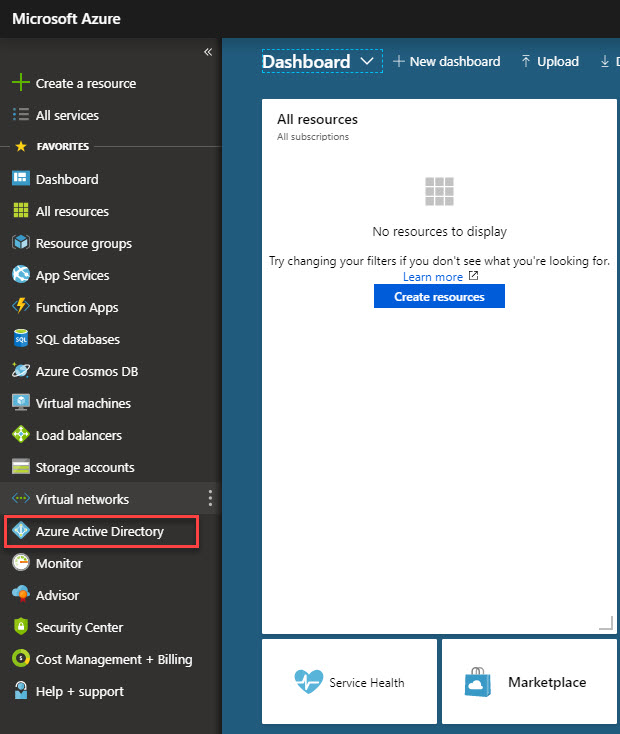
1. Log in to Azure portal https://portal.azure.com as global administrator
2. Click on Azure Active Directory
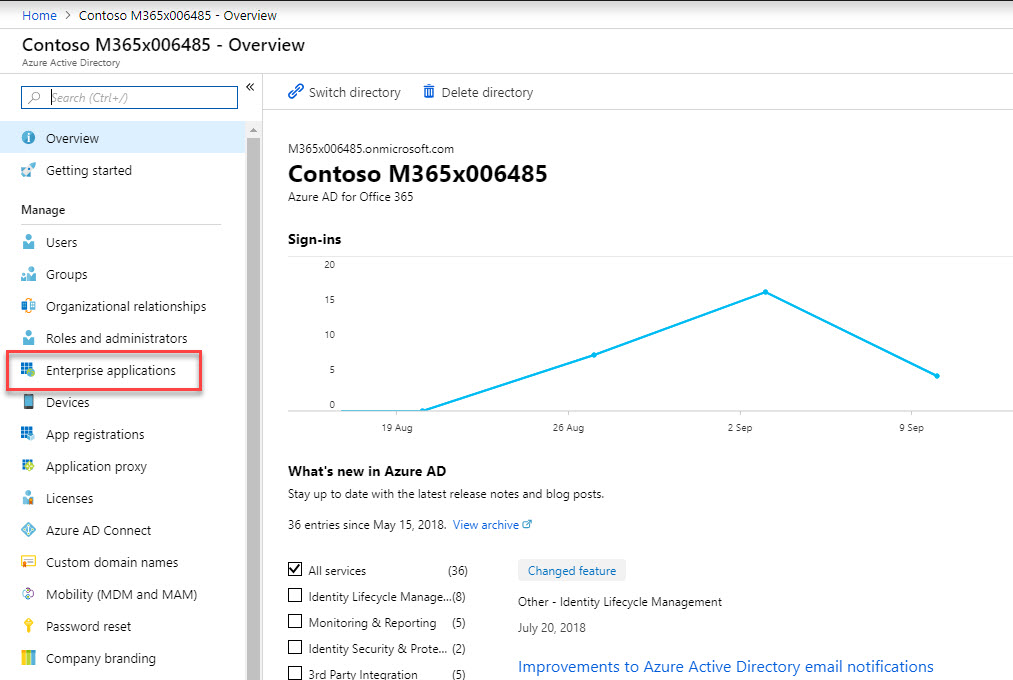
3. Then click on Enterprise Applications
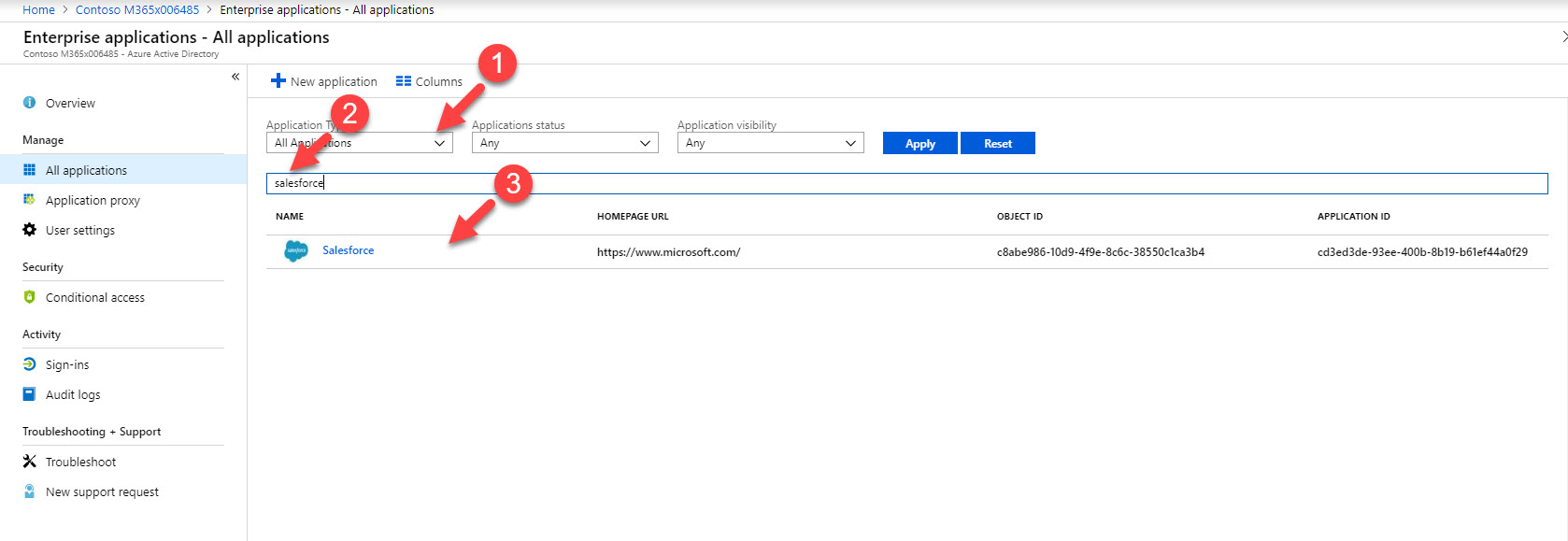
4. Search for Salesforce under All applications and click on it. Note – If it is not existing app, you need to go and add app first and configure it for azure ad sso.
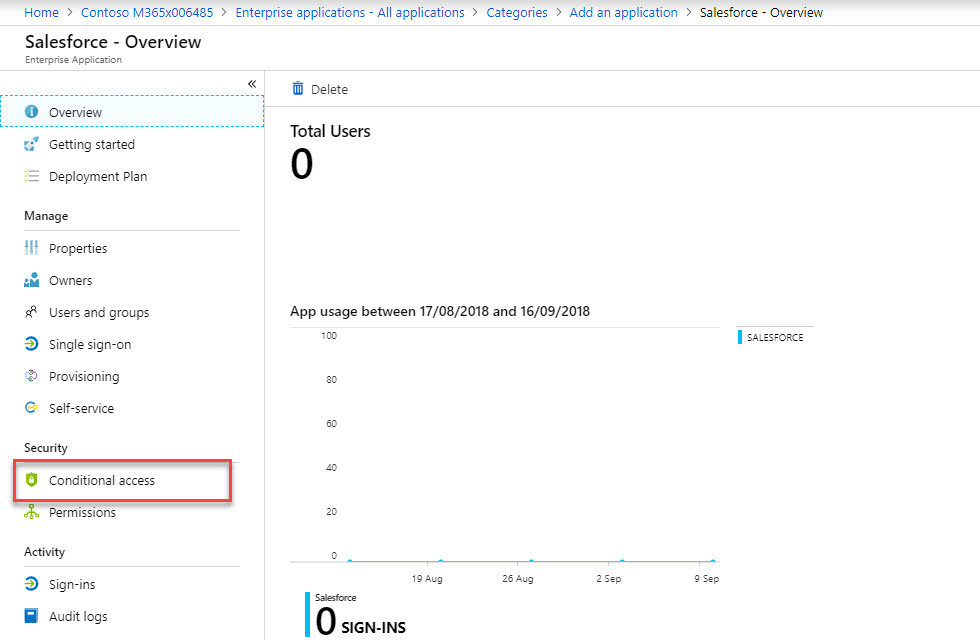
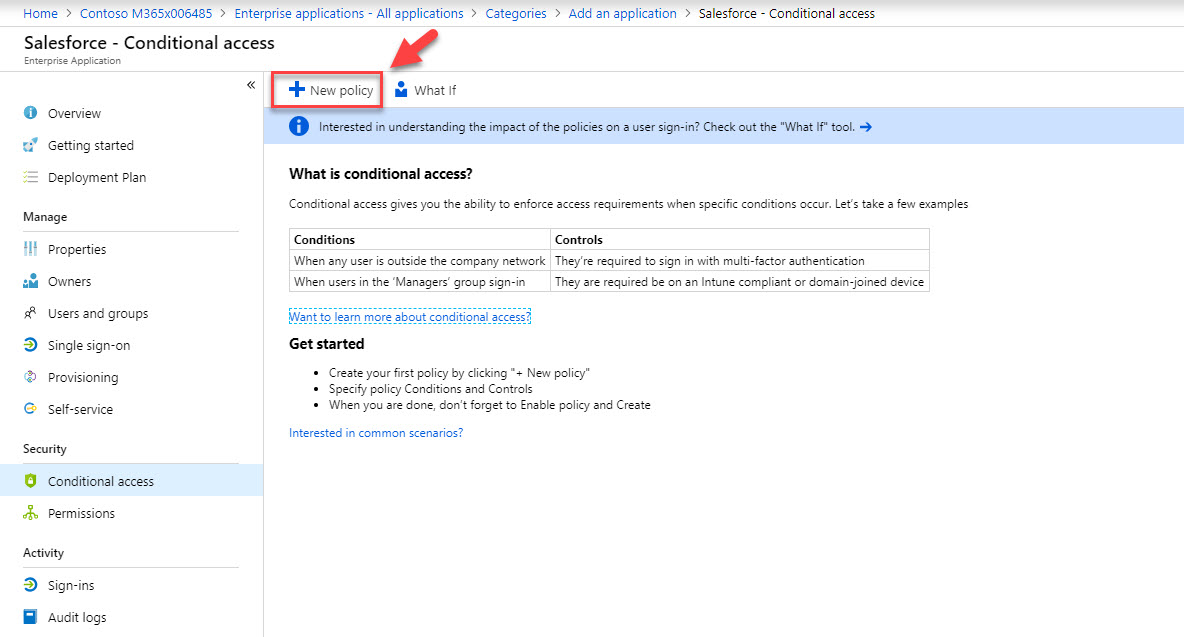
5. Then click on Conditional access
6. Click on + New Policy
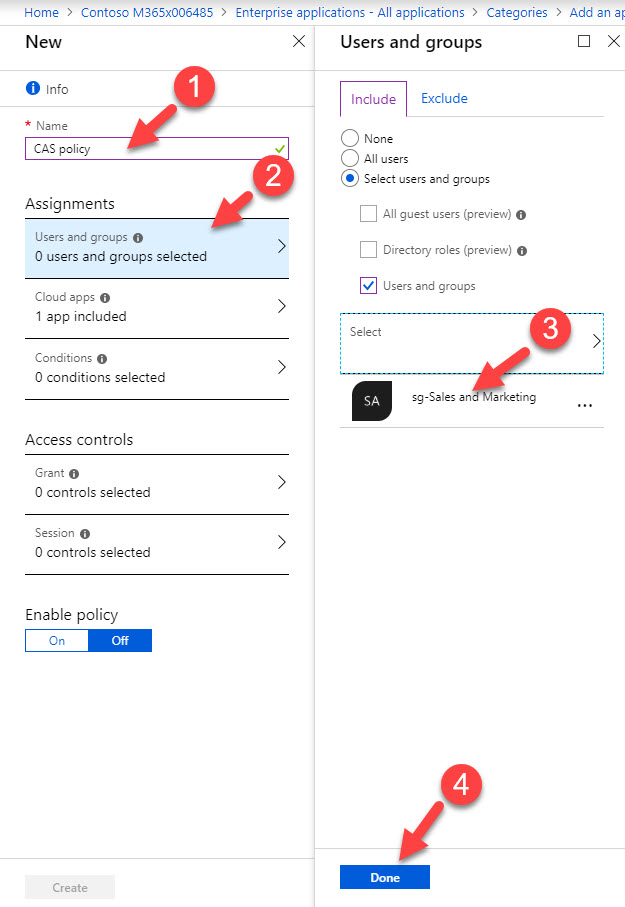
7. Type name for the policy in new window. Then click on users & groups and select relevant user group for the app. in my demo it is sales & marketing group. at the end click on Done to complete the selection.
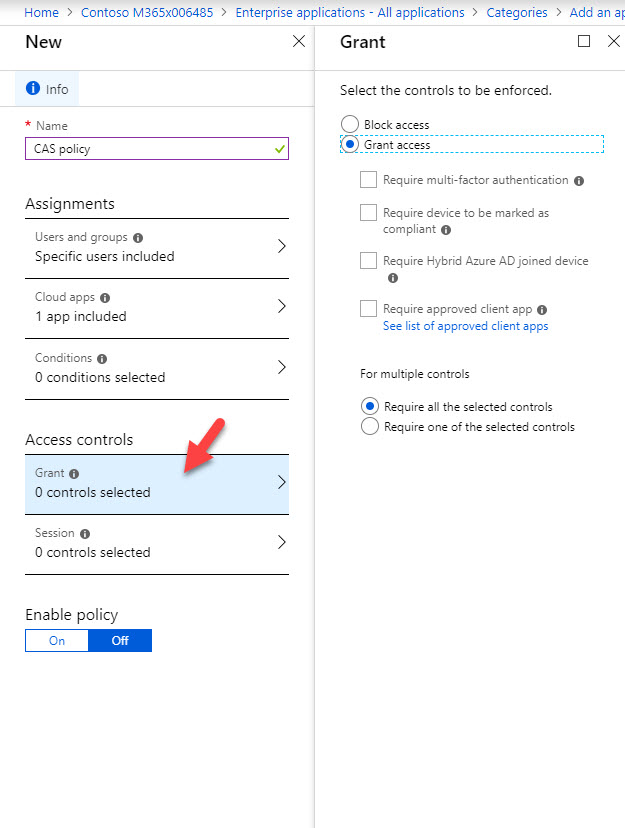
8. Click on Grant under access controls and make sure default Grant access settings selected.
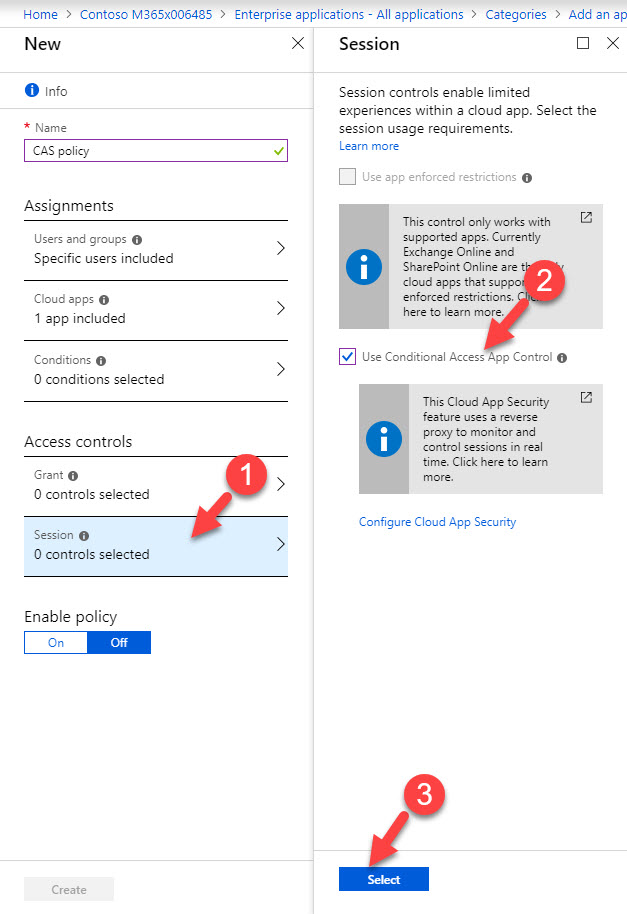
9. Under the sessions select Use conditional access app control .
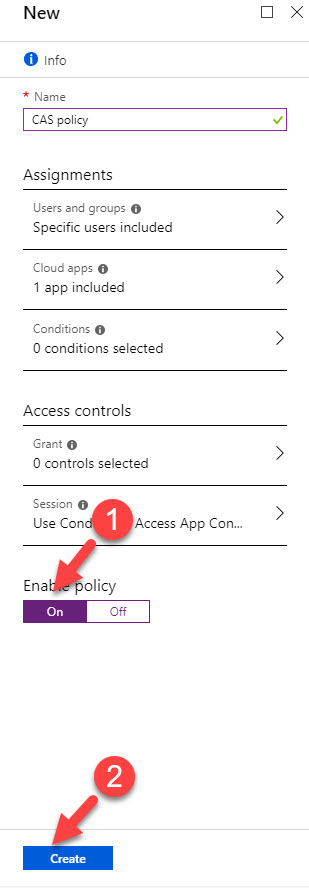
10. At the end click On under Enable policy. Then click on Create to complete the policy.
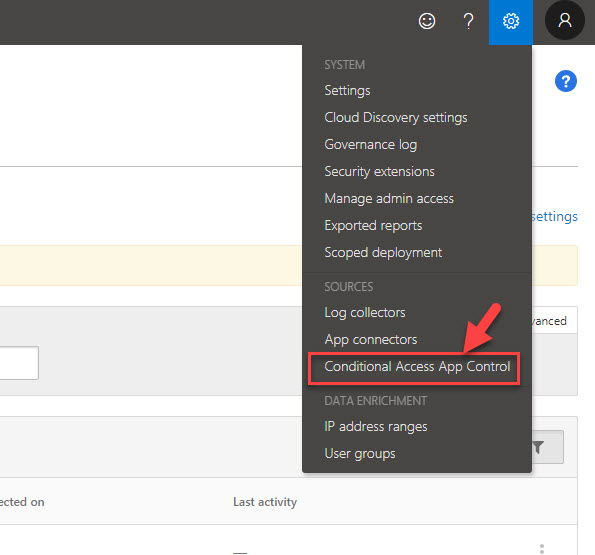
11. Then go to https://portal.cloudappsecurity.com and log in as global admin.
12. Once logged in, click on settings and go to Conditional access app control
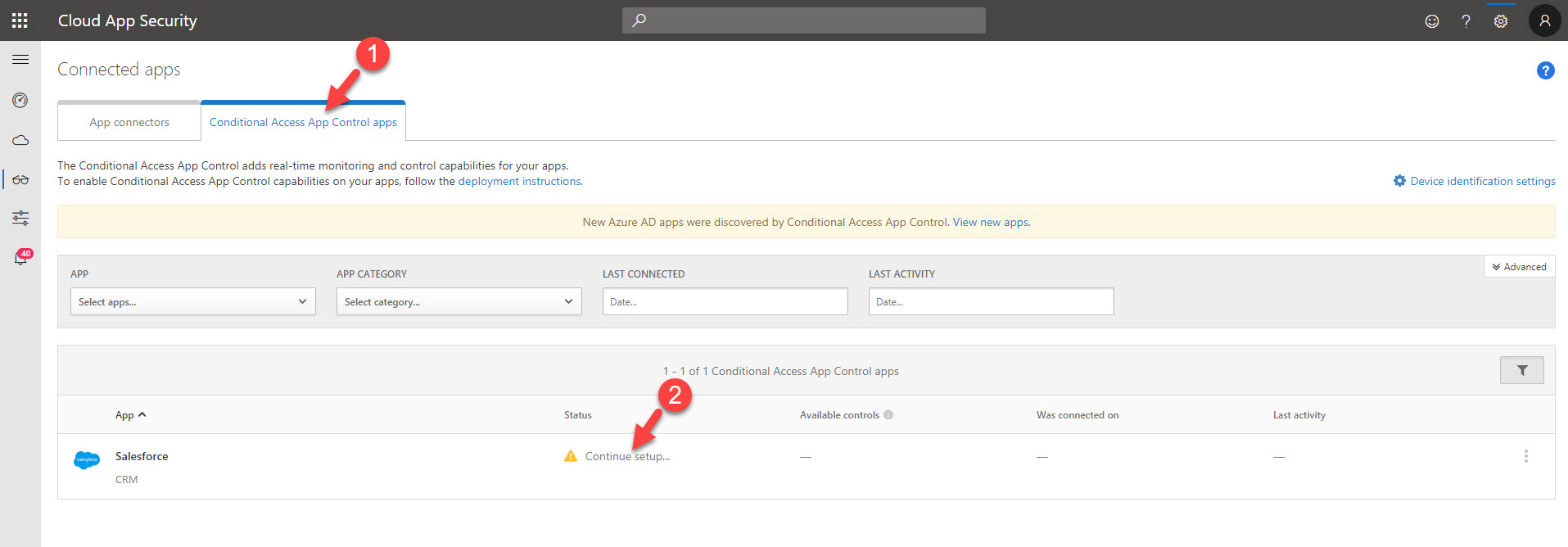
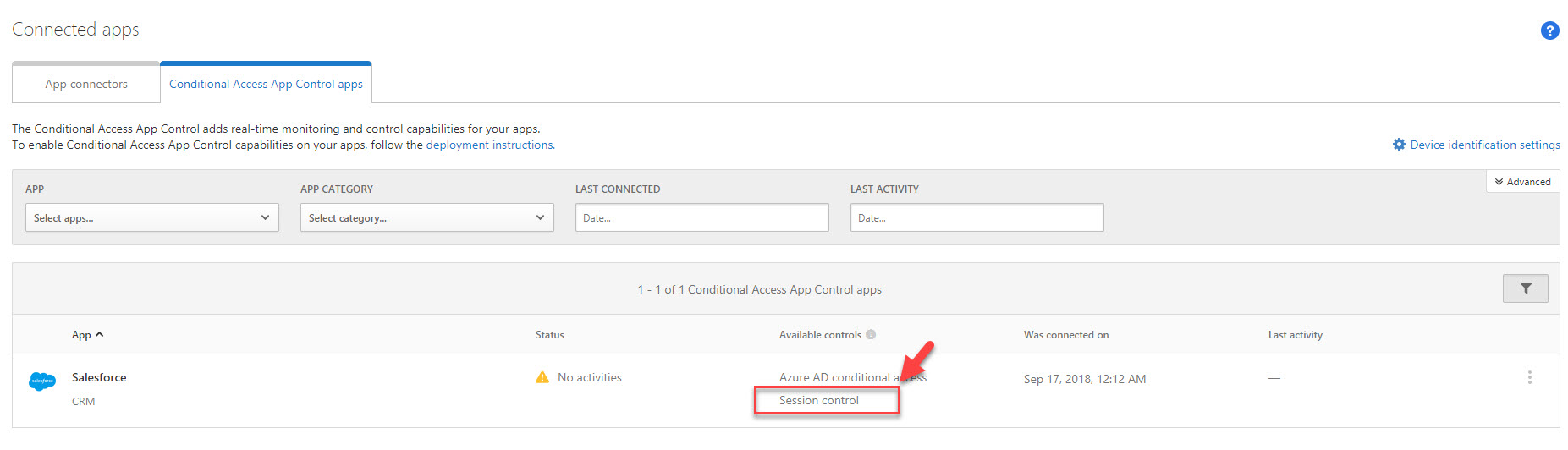
13. In new window click on Conditional Access App Control apps tab. There we can see it discovered sales force app. Please note once you configured the initial policy under azure AD, you need to log in to sales force via https://myapps.microsoft.com . Then only it will trigger the update.
Then click on Continue setup…. link.
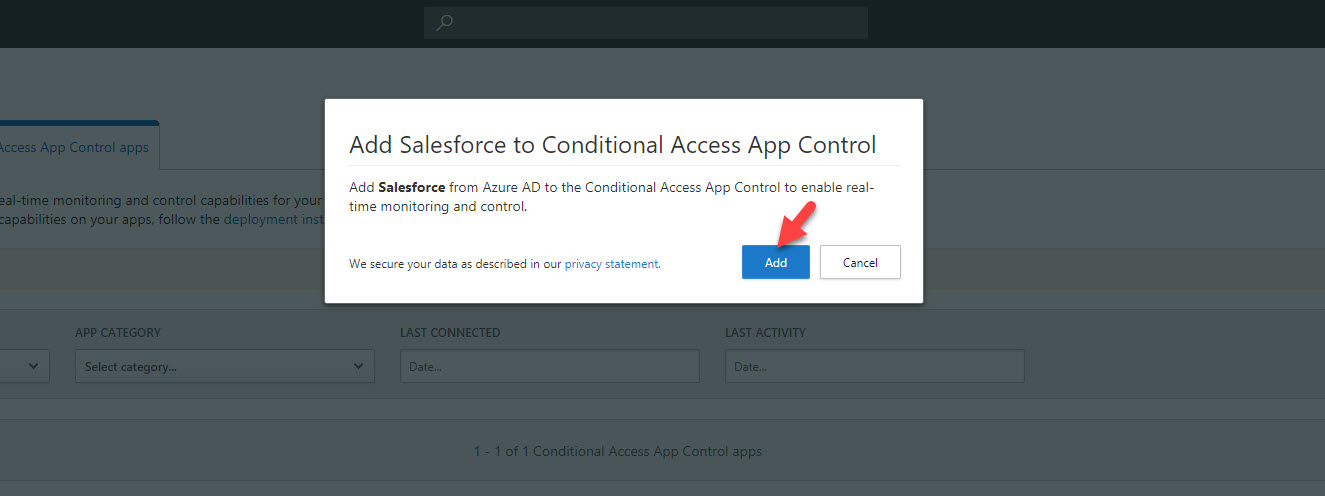
14. It will issue a pop-up. Click on Add to proceed.
15. Then under available controls, click on session control.
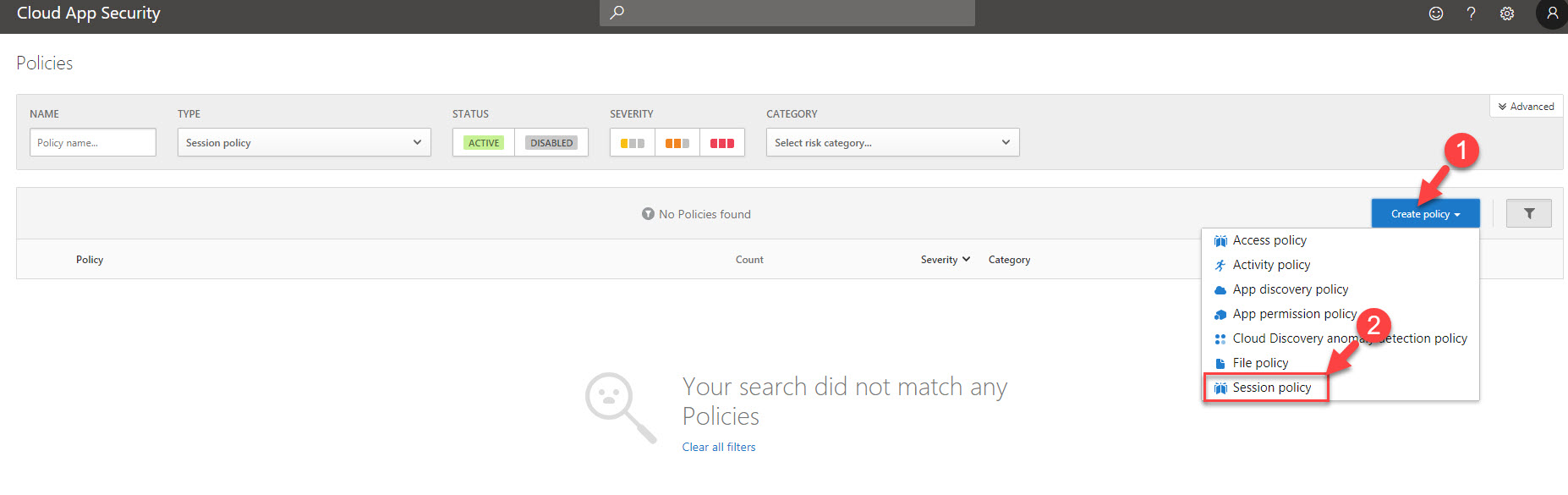
16. In new window, click on create policy drop down and select session policy
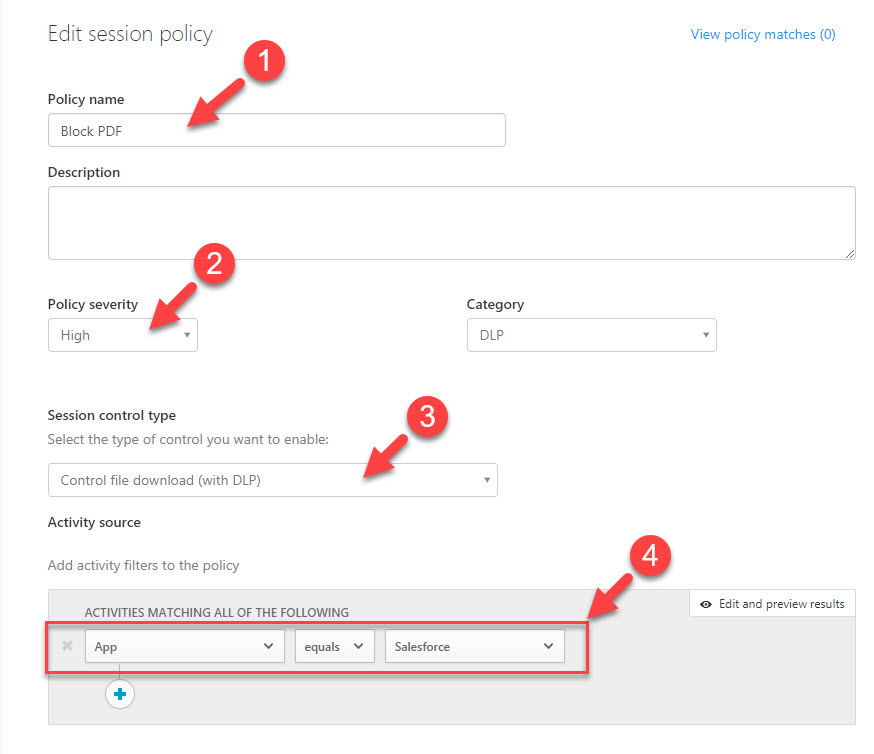
17. In policy window, type name for policy first. Then change policy severity to High. Change session control type to control file download.
Then under activity filters to the policy, set app equals to salesforce.
Same time remove any other filter in that section.
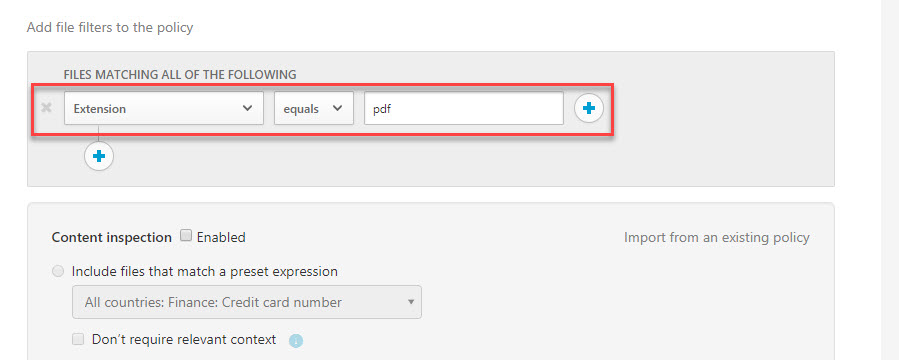
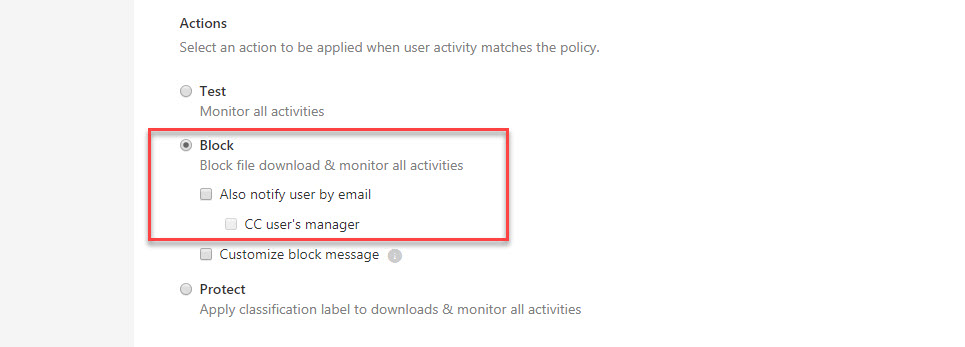
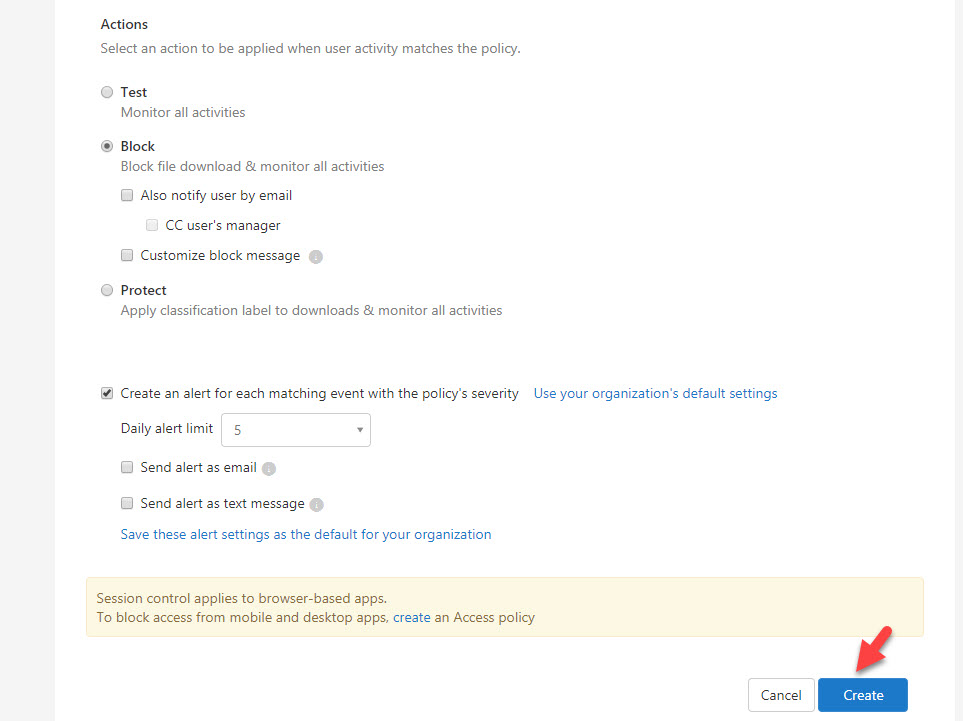
18. Then under file filters to the policy, set extension equals to pdf. At last select block under actions.
19. At the end click on create to setup the policy.
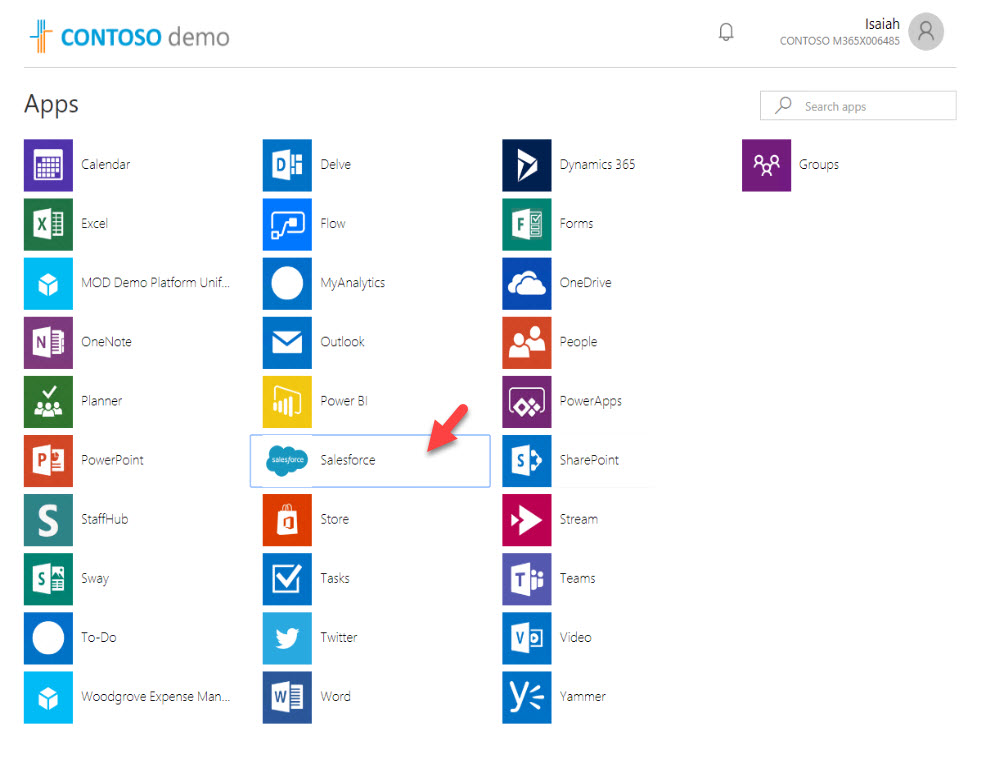
20. According to above policy, if a user trying to download pdf file under salesforce app, it will be blocked. So now it’s time for testing. I logged in to https://myapps.microsoft.com as a user from sales team. Then I click on salesforce app to launch it.
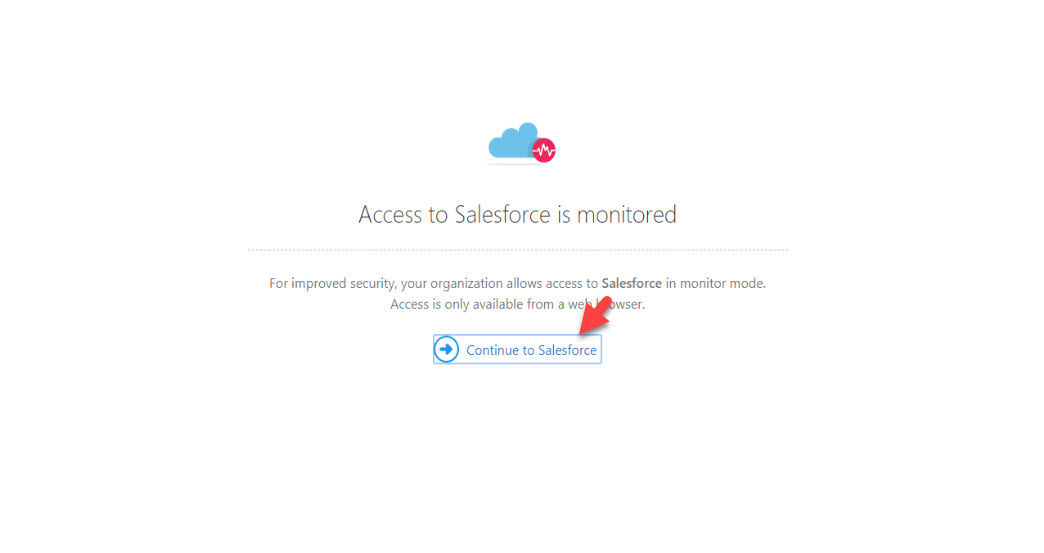
21. In home page, it says access to salesforce is monitored. Click on continue to salesforce.
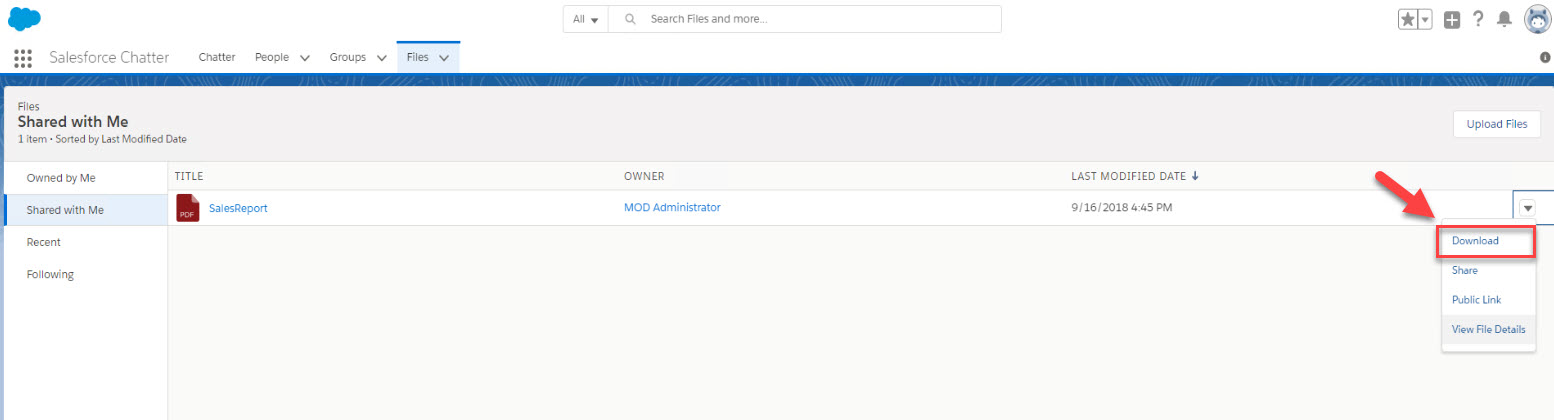
22. Under files, I have a pdf file shared by admin. I click on download option.
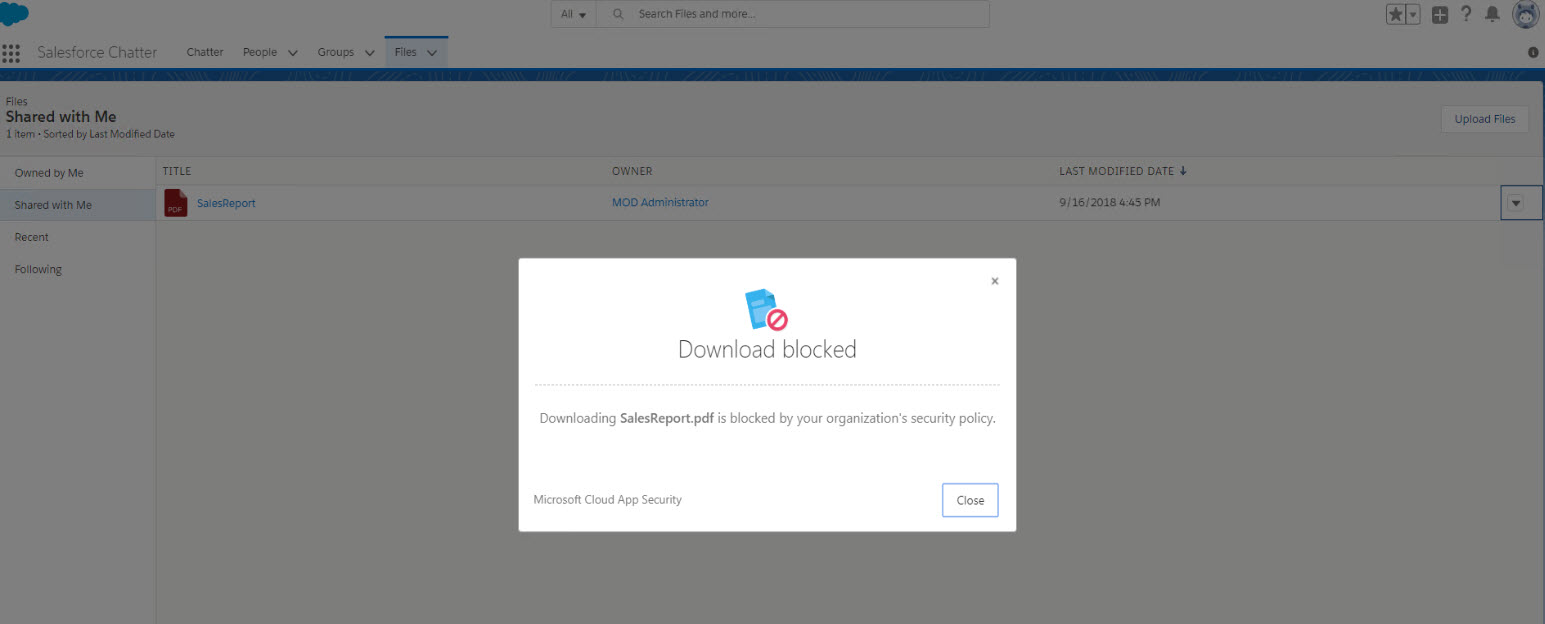
23. As expected, I receive download blocked message.
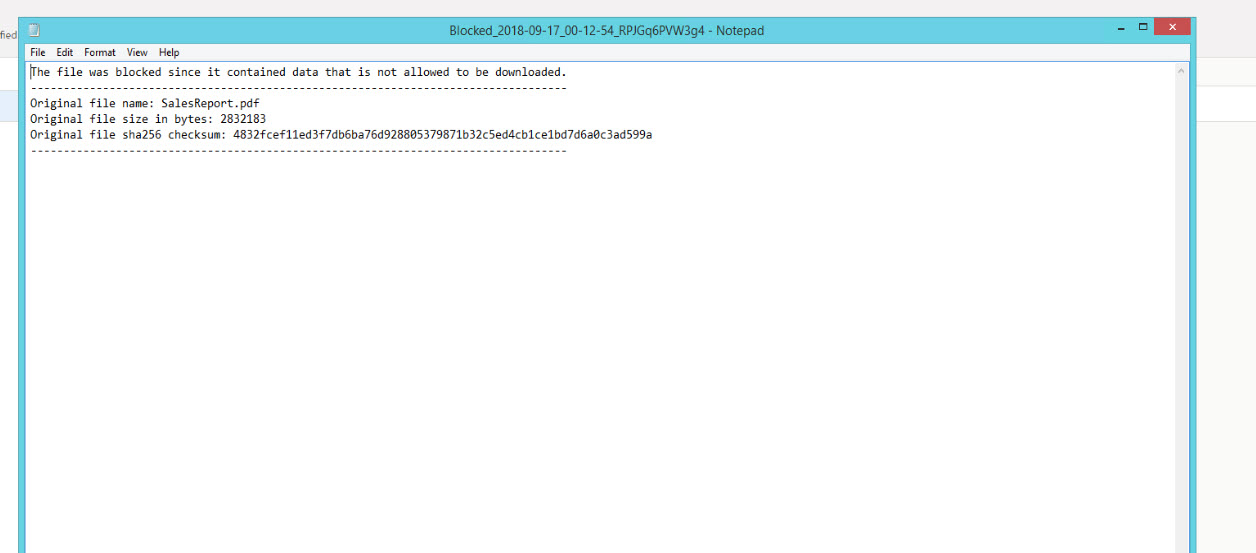
24. Also, it downloads a .txt file same time which contain details of the block.
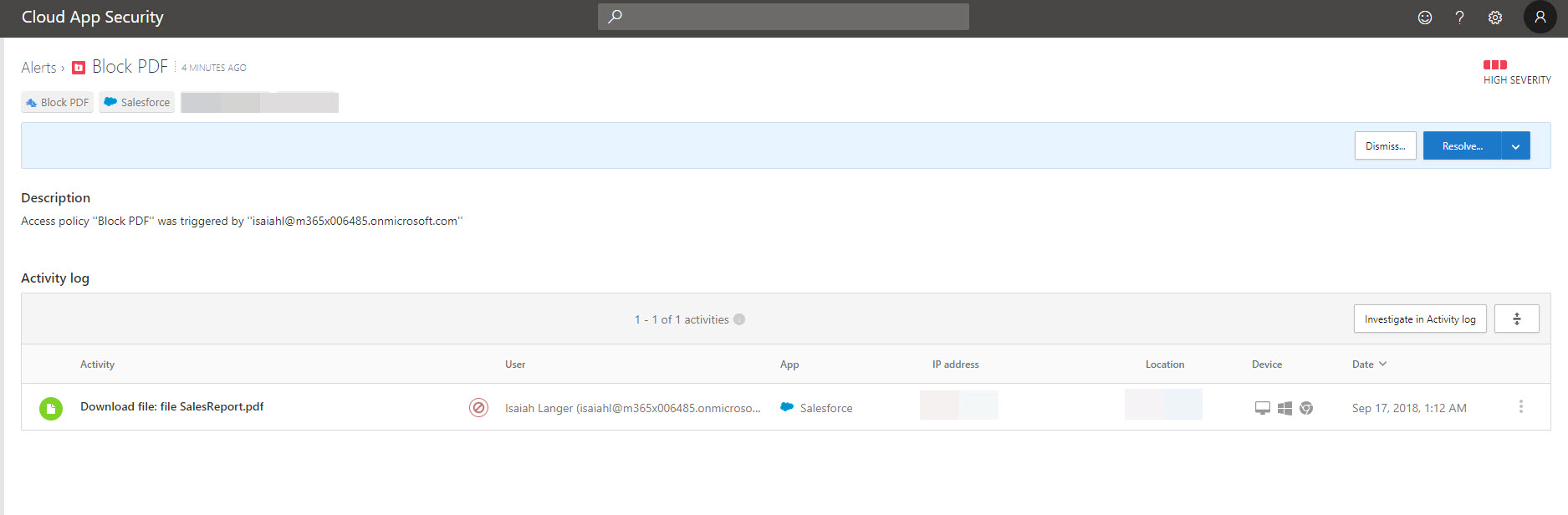
25. In cloud app security logs, we can see detail information related to file block.
This marks the end of this blog post. Hope now you have better understanding how we can protect cloud app content further with cloud app security. If you have any further questions feel free to contact me on rebeladm@live.com also follow me on twitter @rebeladm to get updates about new blog posts.