Disk encryption is a basic data protection method for physical & virtual hard disks. It falls under physical data security and it prevents data breaches from stolen hard disks (physical & virtual). If it is a Windows machine, we can simply use BitLocker for disk encryption. Also, there are other third-party vendors such as Thales e-Security which provides disk encryption solutions for organizations.
Similar to on-premises Windows servers and computers, we can use BitLocker to encrypt Windows VM running on Azure. For Linux VMs, we can use DM-Crypt to encrypt virtual disks. More details about BitLocker is available on https://docs.microsoft.com/en-gb/windows/security/information-protection/bitlocker/bitlocker-overview. Azure VM encryption uses the Azure Key Vault to store encryption keys and secrets.
In this demo, I am going to demonstrate how to encrypt Azure VM using BitLocker. For the configuration process, I will be using PowerShell. Therefore, please make sure you have Azure PowerShell module installed. More info about it can find under https://docs.microsoft.com/en-us/powershell/azure/install-az-ps?view=azps-2.6.0
Setup Resource Group
The first step of the configuration is to create a new resource group.
To do that,
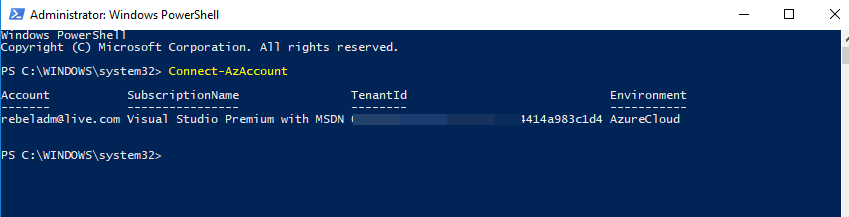
1. Launch PowerShell console and connect to Azure using Connect-AzAccount
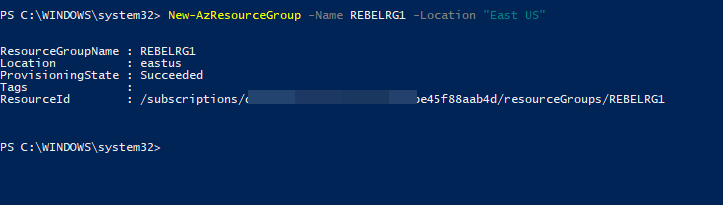
2. Then create a new resource group using,
New-AzResourceGroup -Name REBELRG1 -Location "East US"
In the above, REBELRG1 is the resource group name and East US is the resource group location.
Configure Azure Key Vault
Next, we need to create a new key vault and encryption key.
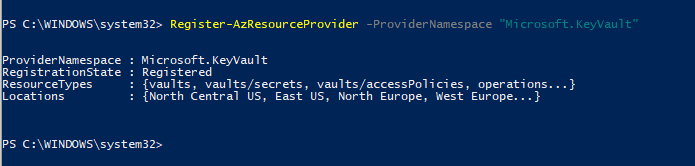
1. As the first step, let's go ahead and enable Azure Key Vault provider within the subscription by using,
Register-AzResourceProvider -ProviderNamespace "Microsoft.KeyVault"
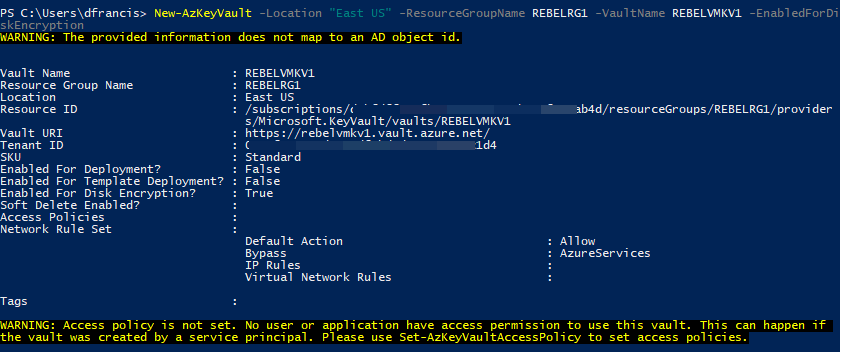
2. Then, we go ahead with Azure Vault setup,
New-AzKeyVault -Location "East US" -ResourceGroupName REBELRG1 -VaultName REBELVMKV1 -EnabledForDiskEncryption
In the above, REBELVMKV1 is the key vault name and it is created under REBELRG1 resource group which we created in the previous step. -EnabledForDiskEncryption is used to prepare the key vault to use with disk encryption.
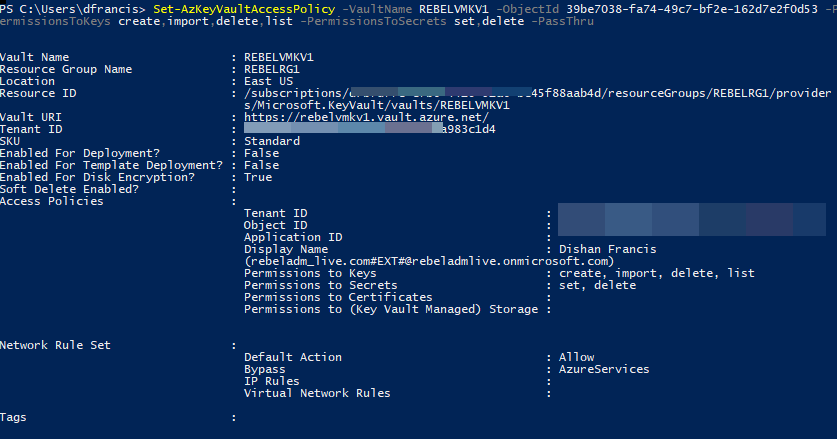
3. Then we need to create access policy so currently logged in user can create encryption keys.
Set-AzKeyVaultAccessPolicy -VaultName REBELVMKV1 -ObjectId xxxxxxxxxxxxxxxx -PermissionsToKeys create,import,delete,list -PermissionsToSecrets set,delete -PassThru
In above objectid should replace with the actual objectid value of the currently logged in global admin account. In here -PermissionsToKeys define the permissions allocated for keys and -PermissionsToSecrets defines the permissions allocated for secrets.
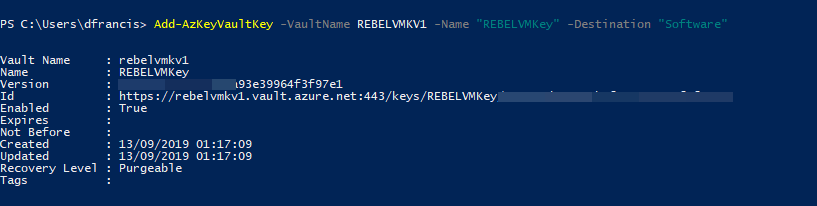
4. Now we need a new encryption key to use with disk encryption.
Add-AzKeyVaultKey -VaultName REBELVMKV1 -Name "REBELVMKey" -Destination "Software"
In the above, REBELVMKey is the key name. -Destination is defined as Software as we creating the standard encryption key. If required it can be set to Hardware Security Model (HSM) but it comes with additional cost.
Create VM
In this demo, I am going to create a new VM for encryption testing. It is not a must; we still can encrypt any existing VM.
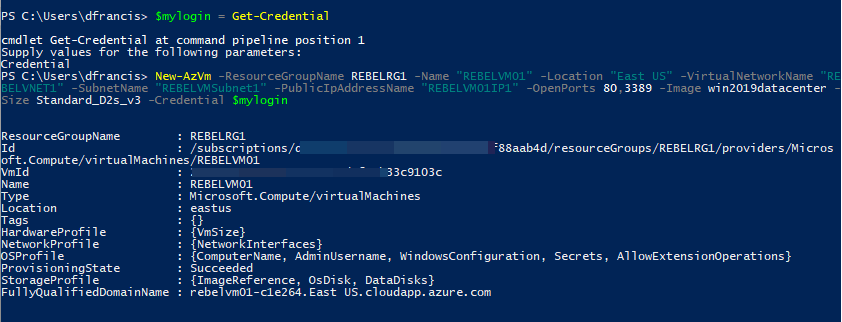
To create new VM I am using,
$mylogin = Get-Credential
New-AzVm -ResourceGroupName REBELRG1 -Name "REBELVM01" -Location "East US" -VirtualNetworkName "REBELVNET1" -SubnetName "REBELVMSubnet1" -PublicIpAddressName "REBELVM01IP1" -OpenPorts 80,3389 -Image win2019datacenter -Size Standard_D2s_v3 -Credential $mylogin
In the above, REBELVM01 is the VM name. It is running windows server 2019 data center edition. I have specified it using -Image parameter. It also using Standard_D2s_v3 vm size.
Encrypt VM
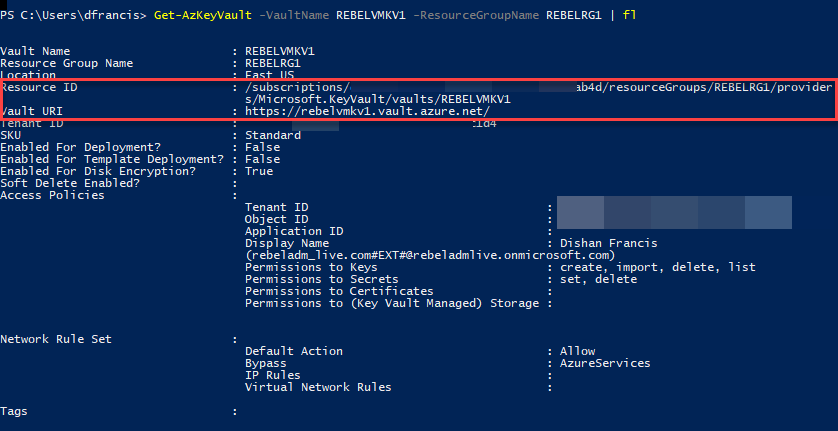
The next step of the configuration is to encrypt the VM. To do that we need the following values,
1. Azure Key Vault Resource ID
2. Azure Key Vault URI
3. Azure Key vault key ID
We can find above values using,
Get-AzKeyVault -VaultName REBELVMKV1 -ResourceGroupName REBELRG1 | fl
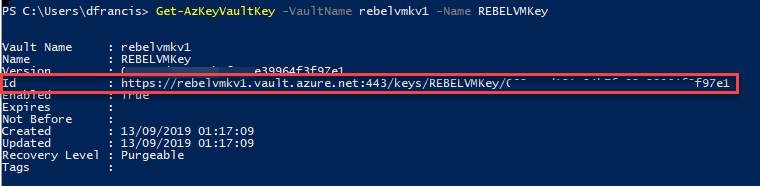
Get-AzKeyVaultKey -VaultName rebelvmkv1 -Name REBELVMKey
[su_note]You will be required GET permissions to retrieve this key value. you have to update it under access policy properties. Or else you also can find this info from the output of key creation command we used in the previous step. [/su_note]
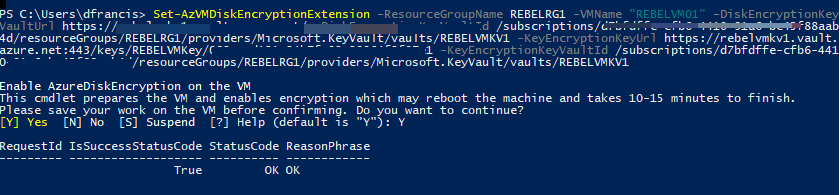
Finally, we can encrypt the VM using,
Set-AzVMDiskEncryptionExtension -ResourceGroupName REBELRG1 -VMName "REBELVM01" -DiskEncryptionKeyVaultUrl (value of Azure Key Vault URI) -DiskEncryptionKeyVaultId (value of Azure Key Vault Resource ID) -KeyEncryptionKeyUrl (value of Azure Key vault key ID) -KeyEncryptionKeyVaultId (value of Azure Key Vault Resource ID)
In above, replace the parameter values according to your setup.
Once encryption is completed, VM will be rebooted.
Verifications
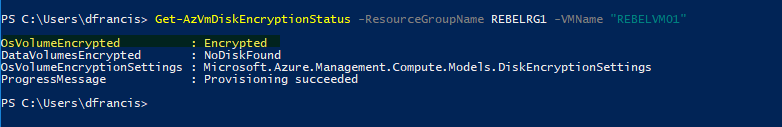
Once the reboot is completed, we can verify the encryption status using,
Get-AzVmDiskEncryptionStatus -ResourceGroupName REBELRG1 -VMName "REBELVM01"
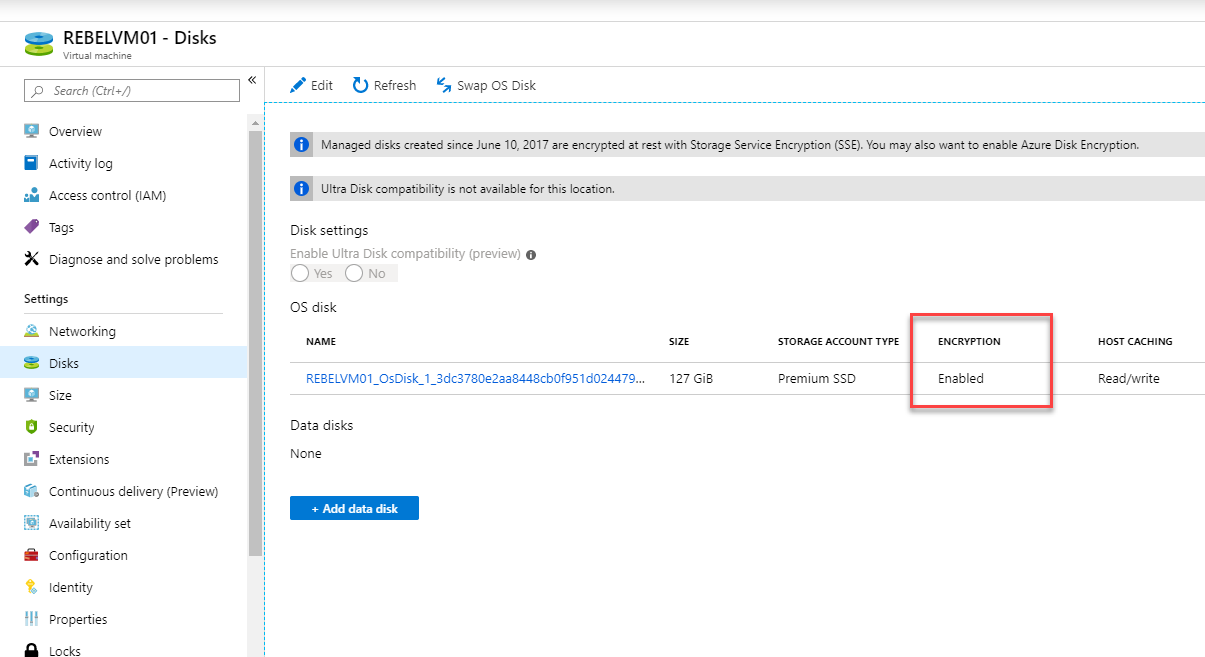
Also, when I go to VM properties | Disks, I can see encryption is enabled as expected.
As we can see the encryption is working as expected. This marks the end of this blog post. If you have any further questions feel free to contact me on rebeladm@live.com also follow me on twitter @rebeladm to get updates about new blog posts.



1 Comment