Happy New Year to all my blog reader! It’s been quite time for the blog as I was stuck on some projects. With New Year I am back in blogging.
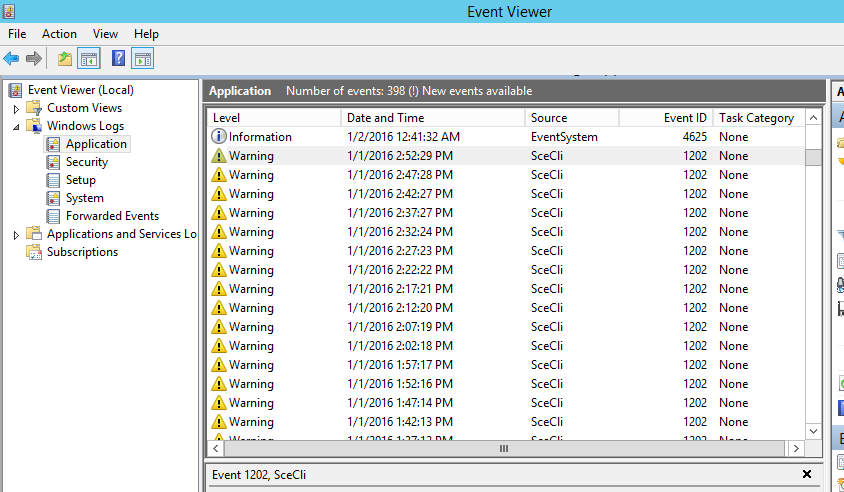
Today I am going to show how to fix the Active directory group policy related error. The relevant event viewer error code is 1202.
It can be in either on domain controllers itself or the local computers. It will be visible in Event viewer > Windows Logs > Application Log
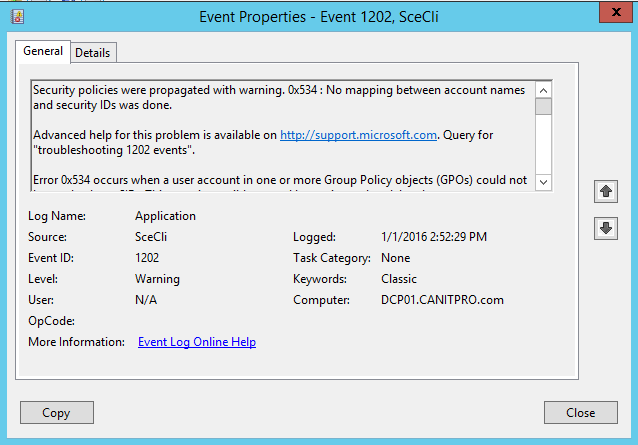
So what is this error about?
As it describes in error it’s saying no mapping between account names and security IDs. Which means there is a GPOs setting which used for domain computers, controllers with orphaned account details. Those accounts couldn’t resolved to correct SID.
How it is possible?
Well there is only two possibilities.
1) The relevant account used in the GPO is removed from AD.
2) Within the GPO the account name is typed incorrectly.
Microsoft done great job on the event log explaining how to fix that error. But let’s see how we really can trigger down the problem.
The first thing we need to do is find out the accounts which have problems with.
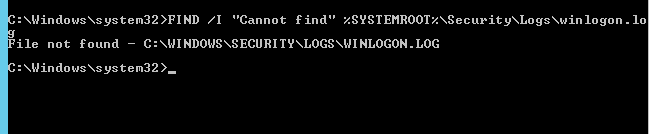
To find it need to run command from the domain controller as domain administrator
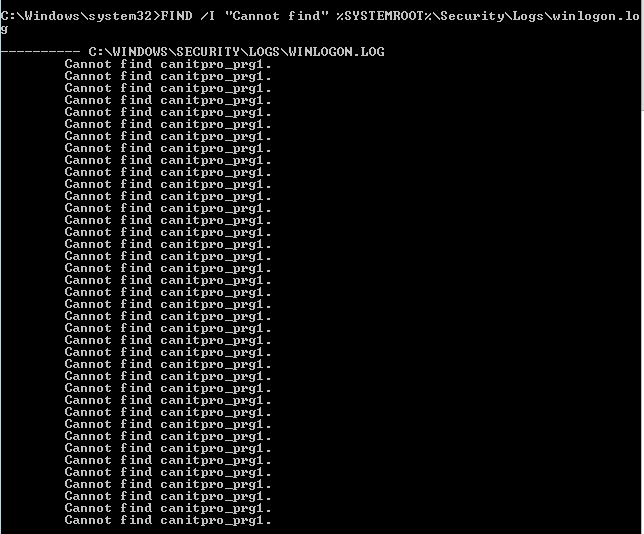
FIND /I "Cannot find" %SYSTEMROOT%\Security\Logs\winlogon.log
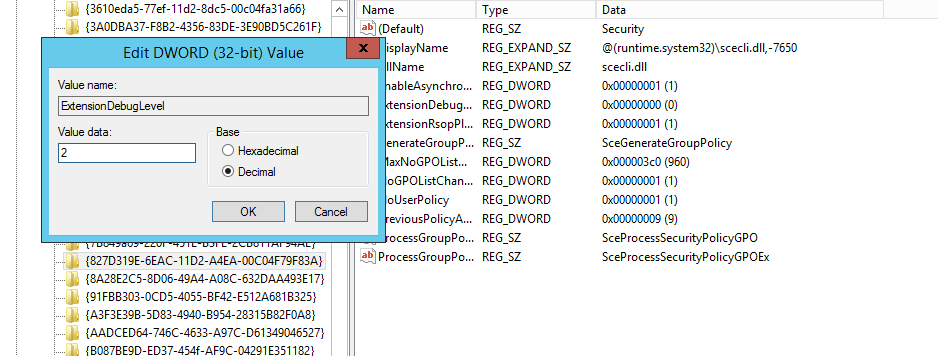
Oh, it is saying no log file. It is because its not enabled. To do it go to regedit,
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions\{827D319E-6EAC-11D2-A4EA-00C04F79F83A}
And then double click on key ExtensionDebugLevel and set it to 2.
If the log is created first time, we need to wait for some time till it collect the logs.
Then let’s try again same command.
This time it shows canitpro_prg1 is the account. So next step is to find where it is used.
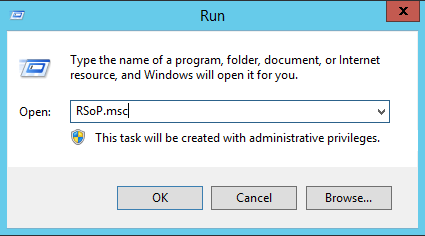
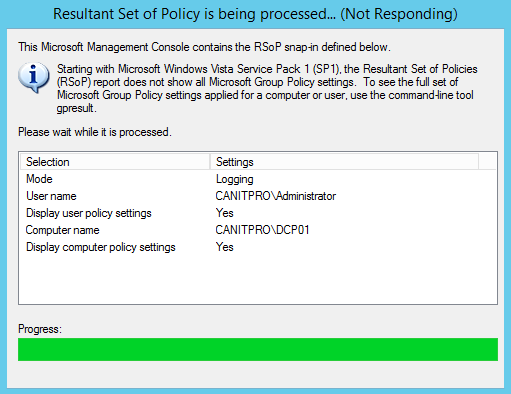
To do it run RSoP (Resultant Set of Policy) mmc to identify the source GPO that contain the problems.
To do it go to Run > RSoP.msc > Enter
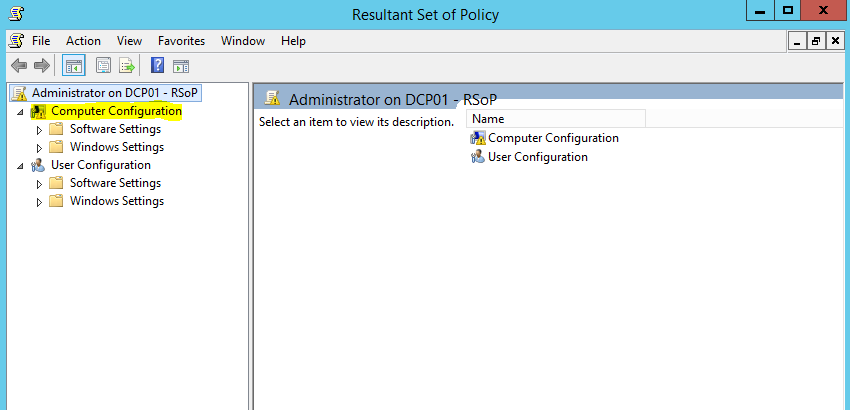
Then in result window it shows problem is stick with the computer configuration
Then when go to Computer Configuration > Security Settings > Local Policies > User Rights Assignment it shows log on as a service got the faulty account applied.
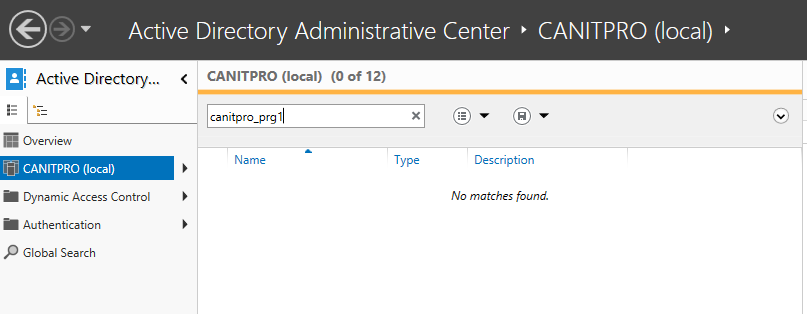
So let’s see if this account exist in AD.
As can see its not existing in AD, the error is clear. To fix the issue we need to remove this account from the list. Once you done that, make sure you run gpupdate /force to apply the new policy setting.
If you have any question about article feel free to contact me on rebeladm@live.com




How about when the same error comes up with in build User Groups like "Authenticated Users" and "Administrators" user groups?
I am getting the same error while running CACLS on "Authenticated Users" group
For those who have changed your own account name through lusrmgr.msc and got this error:
Simply go back to lusrmg.msc and change your account name back to what it was and it will be solved.
hello, this might seem a dumb question as I am only just getting into this, but you say “to fix the issue we need to remove this account from the list” but if it’s not in the list how do you remove. In the log on as a service property box, it is greyed out too.