As per the recent Microsoft Digital Defense Report 2023 (available at https://www.microsoft.com/en-gb/security/security-insider/microsoft-digital-defense-report-2023), it is highlighted that adhering to fundamental security practices still provides protection against approximately 99% of cyberattacks. When delving into these core security recommendations, the foremost among them is the implementation of multifactor authentication (MFA). Microsoft’s official guidance encourages the adoption of MFA for all users, with a few exceptions:
- Break-Glass Accounts: These accounts are reserved for emergency situations, specifically to re-establish access to Azure services.
- Service Accounts and Service Principles: These non-interactive accounts are not directly tied to end users and are typically used in applications or services where MFA cannot be feasibly implemented.
While enabling multifactor authentication for all users may seem straightforward, it can pose challenges within corporate environments. Instead of an across-the-board implementation, organizations may opt for a phased approach, aligning MFA with specific business cases or units. An effective starting point for this multifactor authentication journey is to begin with privileged accounts.
There are two potential methods to achieve this:
- Creating Entra ID Conditional Access Policies for Administrators: Microsoft advises enabling MFA for the following directory roles at a minimum:
- Global Administrator
- Application Administrator
- Authentication Administrator
- Billing Administrator
- Cloud Application Administrator
- Conditional Access Administrator
- Exchange Administrator
- Helpdesk Administrator
- Password Administrator
- Privileged Authentication Administrator
- Privileged Role Administrator
- Security Administrator
- SharePoint Administrator
- User Administrator
A Microsoft Entra ID conditional access policy can be established to enforce multifactor authentication for these roles, activating MFA verification when users engage with the specified roles. It’s worth noting that such a Microsoft Entra ID conditional access policy typically targets “All cloud apps.”
2.Creating Entra ID Conditional Access Policies to Enforce MFA for Admin Portals: In lieu of specific roles, organizations can craft Microsoft Entra ID conditional access policies aimed at administrative portals, thus mandating MFA for users accessing these portals. Admin portals encompass:
- Azure portal
- Exchange admin center
- Microsoft 365 admin center
- Microsoft 365 Defender portal
- Microsoft Entra admin center
- Microsoft Intune admin center
- Microsoft Purview compliance portal
Microsoft will incorporate additional portals into this list over time. The advantage of this approach lies in its limited impact on backend resources and services, such as Microsoft Graph or Azure Resource Manager APIs. This ensures that only the portal itself is subject to MFA enforcement, leaving operations reliant on APIs or PowerShell unaffected.
Once administrators are prepared, they can transition to the first option mentioned, implementing multifactor authentication for all privileged roles. In this blog post, we will explore the process of enforcing MFA for admin portals using Microsoft Entra ID conditional access policies.
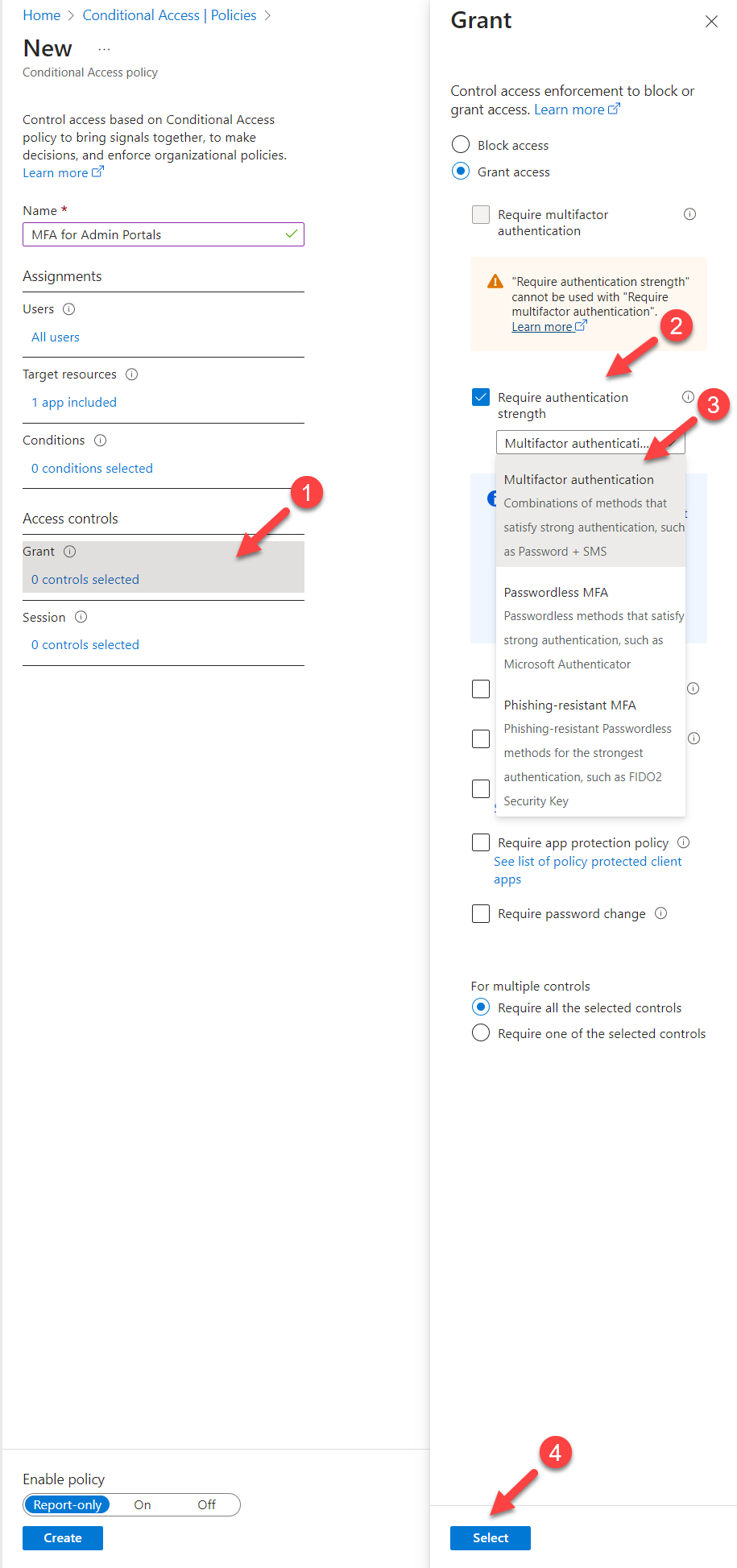
To configure the policy,
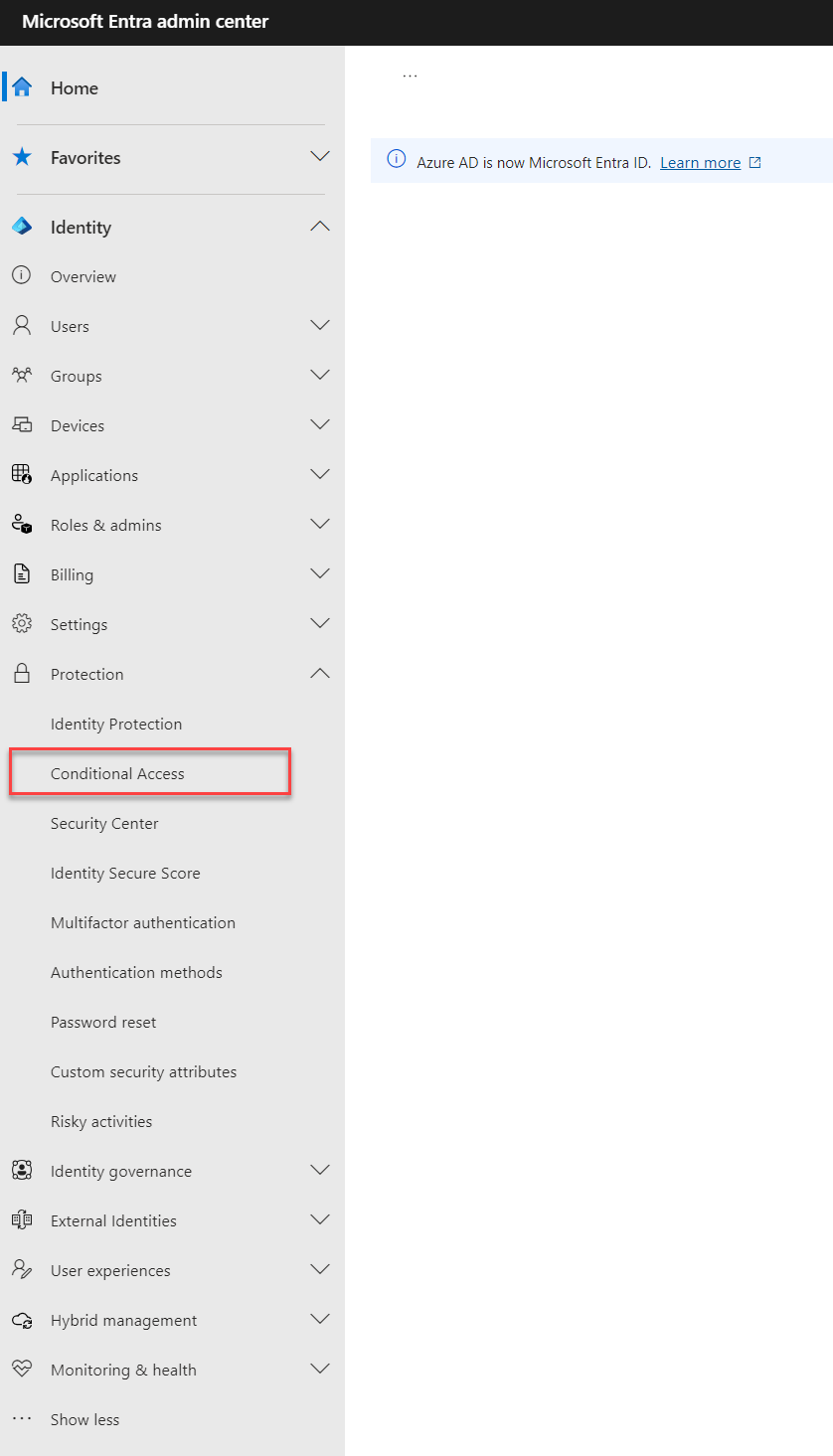
- Log in to Entra Admin Center https://entra.microsoft.com/ as at least a Conditional Access Administrator.
- Go to Protection | Conditional Access
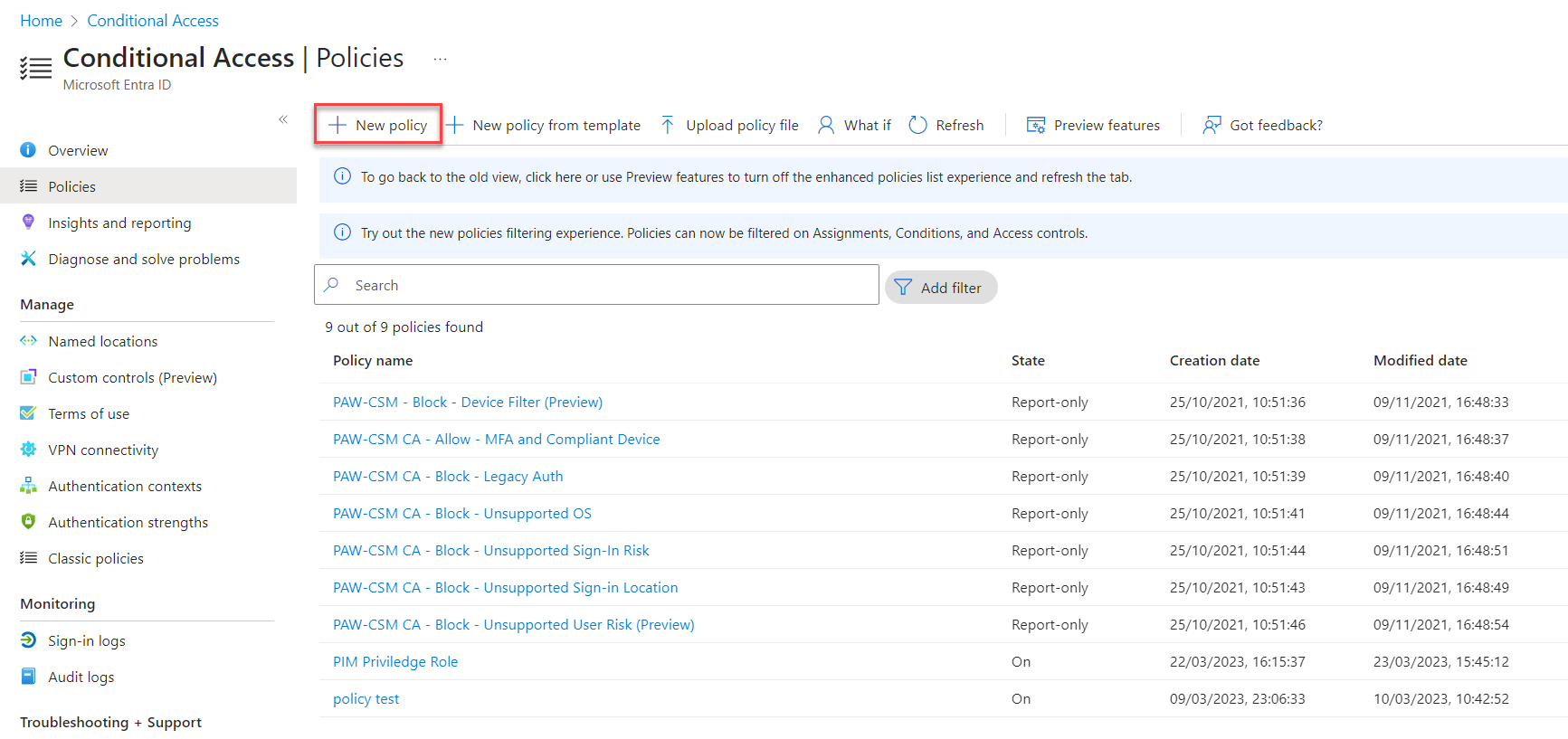
- Then click on Policies | + New policy
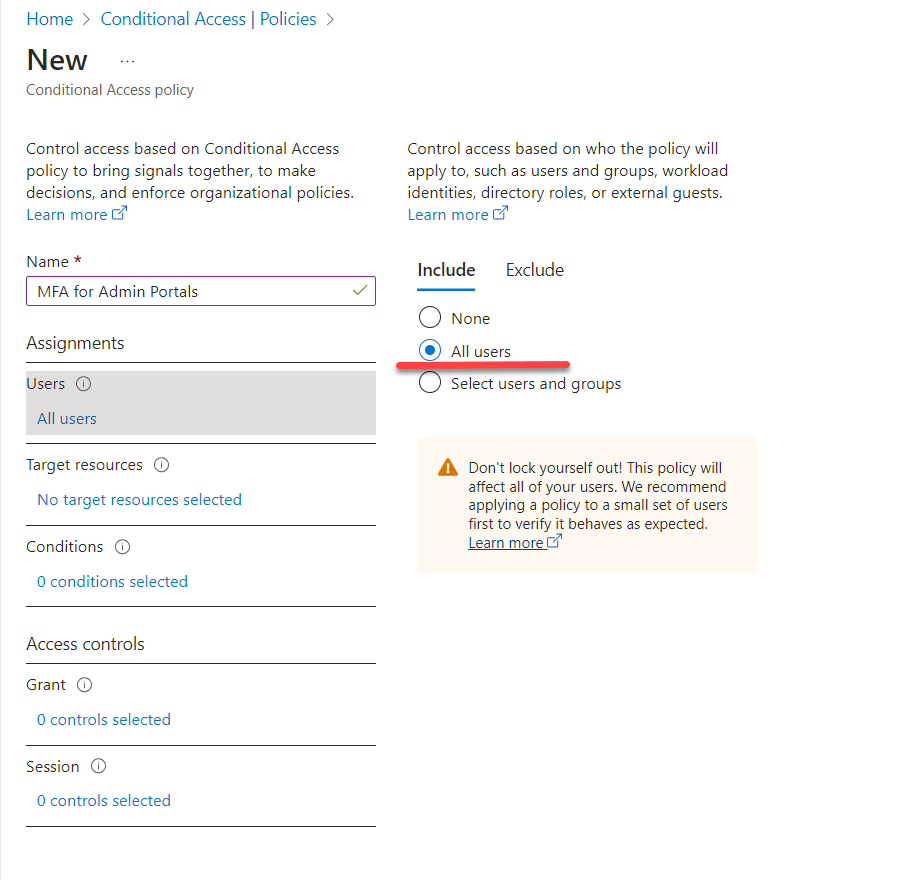
- In the new policy window, type Name for the policy and click on Users
- In this policy, we are going to target all users. So make sure to select All users option.
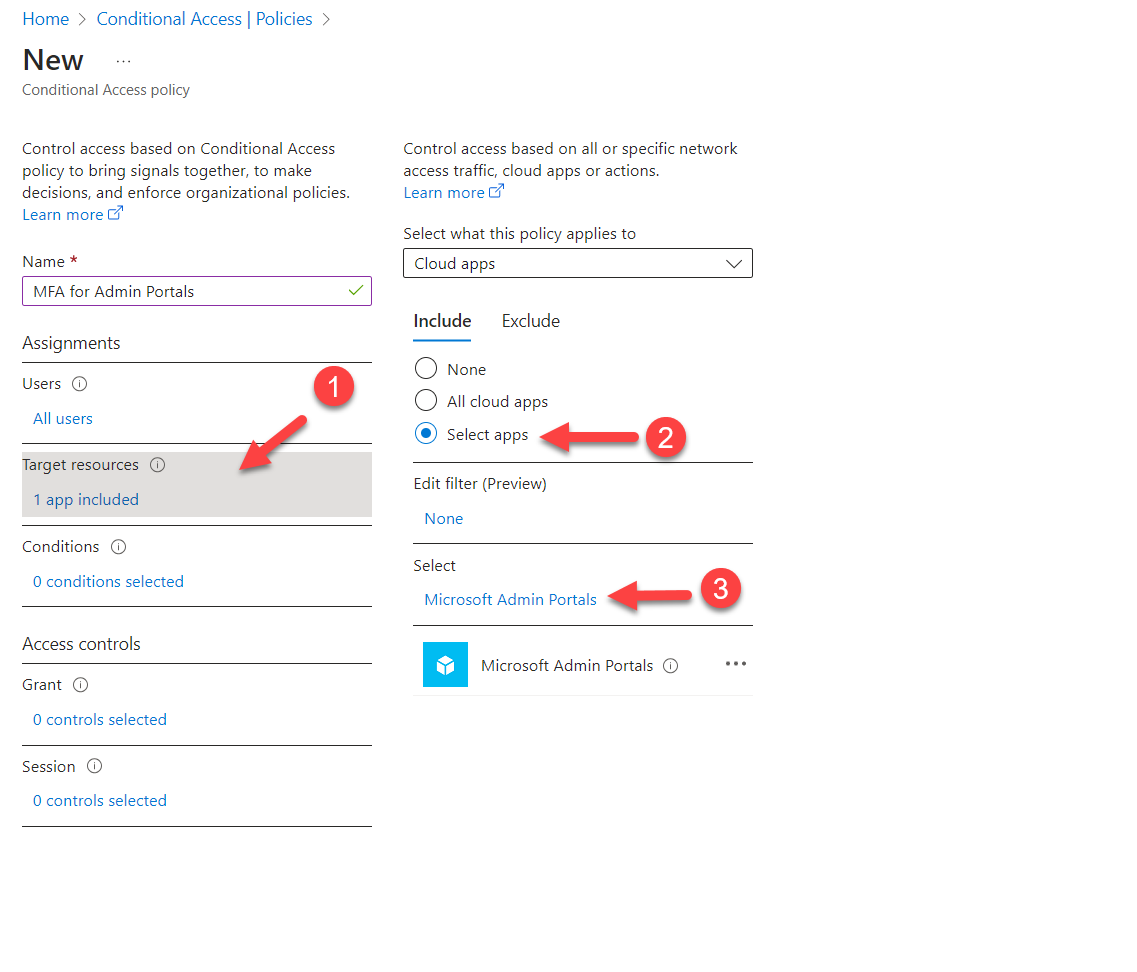
- Then under the Target resources, click on Selected apps | Select, and then from the list select Microsoft Admin Portals.
- The next step of the configuration is to define access control settings. To do that click on Access Control | Grant and then select Required authentication strength. So in there, we have three options to choose from.
- MFA strength
- Passwordless MFA strength
- Phishing-resistant MFA strength
The recommendation is to use Phishing-resistant MFA strength as it provides maximum protection. But that required the use of FIDO2 security key / Windows Hello. To learn more about these options please visit https://learn.microsoft.com/en-us/azure/active-directory/authentication/concept-authentication-strengths#built-in-authentication-strengths
For this demo, I am going to use MFA strength and it is similar to using the Require multifactor authentication setting as it uses the same set of combinations.
-
- Then select On under Enable policy setting and click on Create to finish the policy setup.
This completes the policy setup and let’s do some testing to confirm.
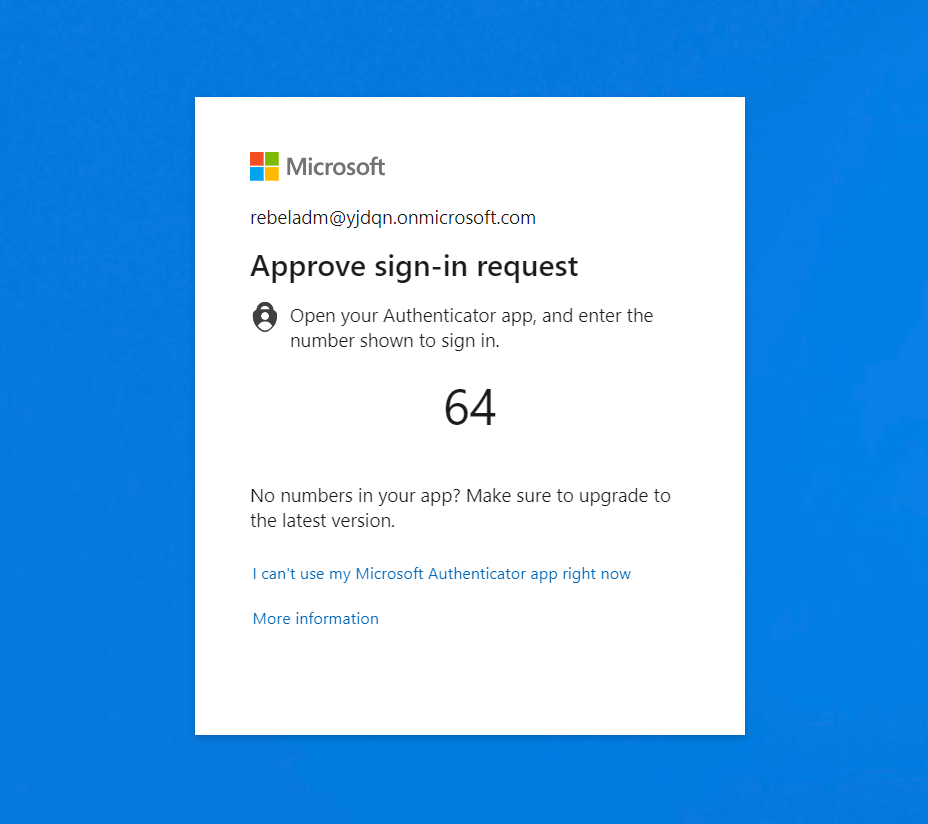
MFA Testing
For testing, I am trying to log in to the entra admin center as Global Admin. As expected it prompted me to MFA.
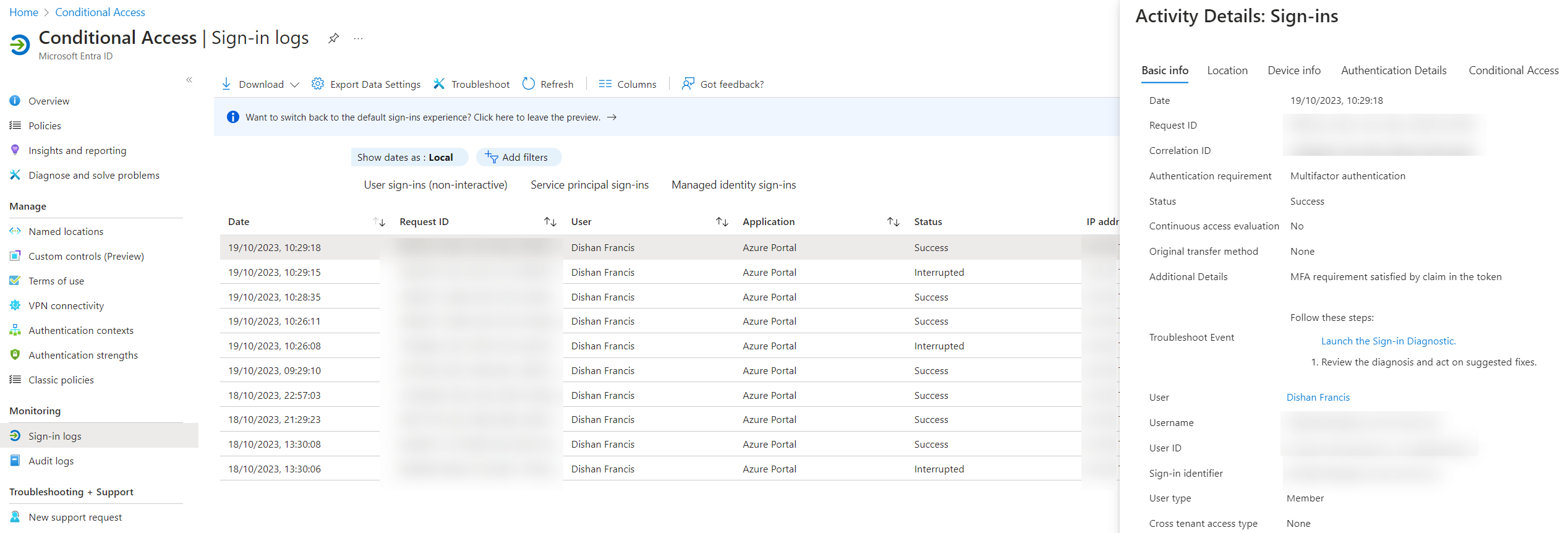
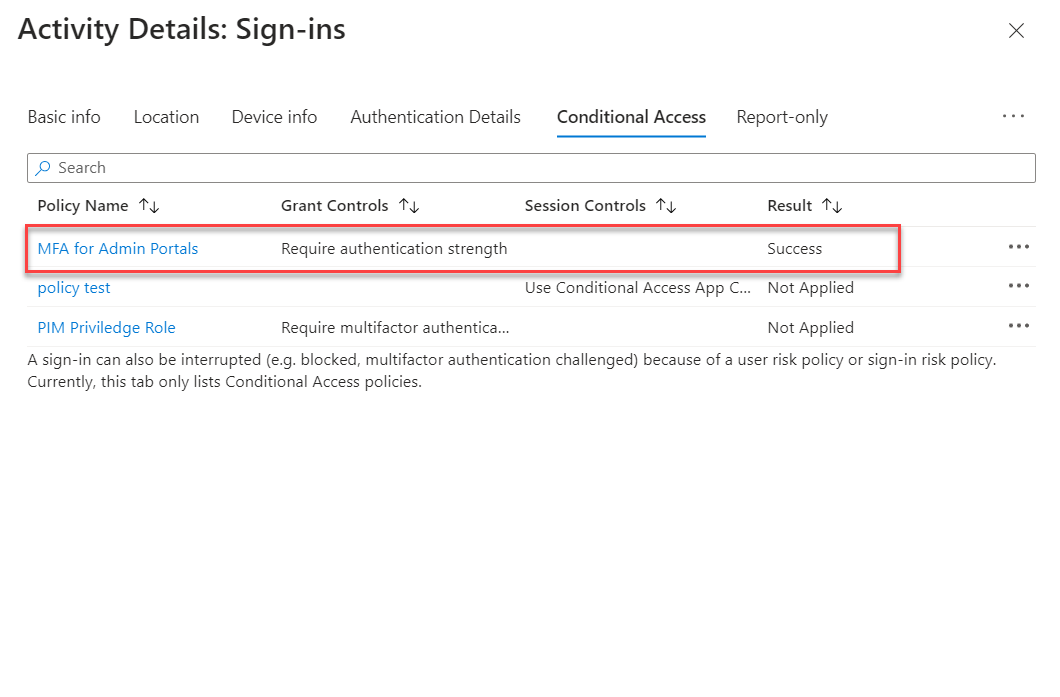
Also under the Sign-in logs, I can see the new policy has been applied.
As we can see now multifactor authentication is enforced for admin portal logins. This marks the end of this blog post and if you have any questions, feel free to reach me at rebeladm@live.com