Windows Server 2008 and Windows Server 2008 R2 Operating system reached the end of their support cycle on the 14th of January 2020. Because of this many organizations wanted to migrate away from these legacy operating systems. End-of-life operating systems have a direct impact on various industry compliances, IT audits, Penetration tests, and so on. Even business does not have a business requirement to upgrade, end of life operating system leaves no choice but to upgrade.
In the past, I did a similar blog post covering migration AD from Windows Server 2008 to Windows Server 2016. Microsoft released Windows Server 2022 recently (Aug 2021) and I thought it good to demonstrate how we can migrate AD from 2008 R2 to the newest. AD migrations from other operating systems (newer than Windows Server 2008R2) also follow a similar process.
What is New in Active Directory?
AD DS’ improvements are bond to its forest and domain functional levels. Upgrading the operating system or adding domain controllers that run Windows Server 2022 to an existing AD infrastructure isn’t going to upgrade the forest and domain functional levels automatically. We need to upgrade it manually once older domain controllers are decommissioned. There was a big difference with Windows Server 2019 when it comes to forest and domain functional levels. With each and every Windows Server release up to Windows Server 2016, had a new forest and domain functional level. But with Windows Server 2019 there were NO new forest or domain functional levels. It is the same with Windows Server 2022. The maximum forest and domain functional level we can choose still is Windows Server 2016.
Active Directory Domain Services was first introduced to the world with Windows Server 2000. For more than 21 years, AD DS helps organizations to manage digital identities. However, the modern access management requirements are complicated. Businesses are using more and more cloud services now. The majority of the workforce is still working from home and accessing sensitive corporate data via unsecured networks. Most software vendors are moving into SaaS model. Cybercrimes are skyrocketing and identity protection is at stake. To address these requirements, we need to go beyond legacy access management. Azure Active Directory is a cloud-based, managed, Identity as a Service (IDaaS) provider, which can provide world-class security, strong authentication, and seamless collaboration. So, it does make sense why there are no significant changes to on-premises AD anymore.
One of the key themes of Windows Server 2022 is “security”. Advanced multi-layer security in Windows Server 2022 provides comprehensive protection against modern threats. This also adds an additional layer of security to roles run on Windows Server 2022 including Active Directory. For more details about these security features please refer to https://docs.microsoft.com/en-us/windows-server/get-started/whats-new-in-windows-server-2022
Active Directory Migration Check List
Migrating FSMO roles to a new server and upgrading forest and domain functional levels doesn’t take more than few minutes but when it comes to migration there are few other things we need to consider. Therefore, I have summarized the AD DS Migration process with the following checklist.
- Evaluate the business requirements for Active Directory migration.
- Perform an audit on the existing Active Directory infrastructure to verify its health.
- Create a detailed implementation plan.
- Prepare the physical/virtual resources for the domain controller.
- Install Windows Server 2022 Standard/Datacenter.
- Patch the servers with the latest Windows updates.
- Assign a dedicated IP address to the domain controller.
- Install the AD DS role.
- Migrate the application and server roles from the existing domain controllers.
- Migrate the FSMO roles to the new domain controllers.
- Add new domain controllers to the existing monitoring system.
- Add new domain controllers to the existing DR solution.
- Decommission the old domain controllers (all).
- Raise the domain and forest functional levels.
- Perform ongoing maintenance (Group Policy review, new-feature implementations, identifying and fixing Active Directory infrastructure issues, and more)
Most Common Questions About Active Directory Migrations
Below I listed some of the most common questions about AD migration,
- Can I keep the same IP address for the PDC? Yes, you can. Active Directory fully supports IP address changes. Once FSMO role migration is completed, you can swap the IP addresses of Domain Controllers.
- Can I downgrade forest/domain functional levels? If you required you can do so but this is not a recommended approach. From Windows Server 2008 R2, we can downgrade forest/domain functional levels.
- Do I need to migrate the DNS role? No, it is part of the AD. When you add a new domain controller, you can make it as a DNS server too.
- Do I need to change SYSVOL replication from FRS to DFS? If your domain is built based on Windows server 2008 or Windows Server 2008 R2, you are already using DFS for SYSVOL replication. If you originally migrated from Windows server 2003, it’s more likely you are still using FRS. In that case, before migration, you need to change the SYSVOL replication method from FRS to DFS. I already have a blog post covering this topic https://www.rebeladmin.com/2015/04/step-by-step-guide-for-upgrading-sysvol-replication-to-dfsr-distributed-file-system-replication/
- Can I keep Windows 2008 R2 Domain Controllers and upgrade forest and domain functional level to Windows Server 2016? No, you can’t. Before forest and domain functional level upgrade, you need to decommission Windows server 2008 R2 domain controllers.
Design topology
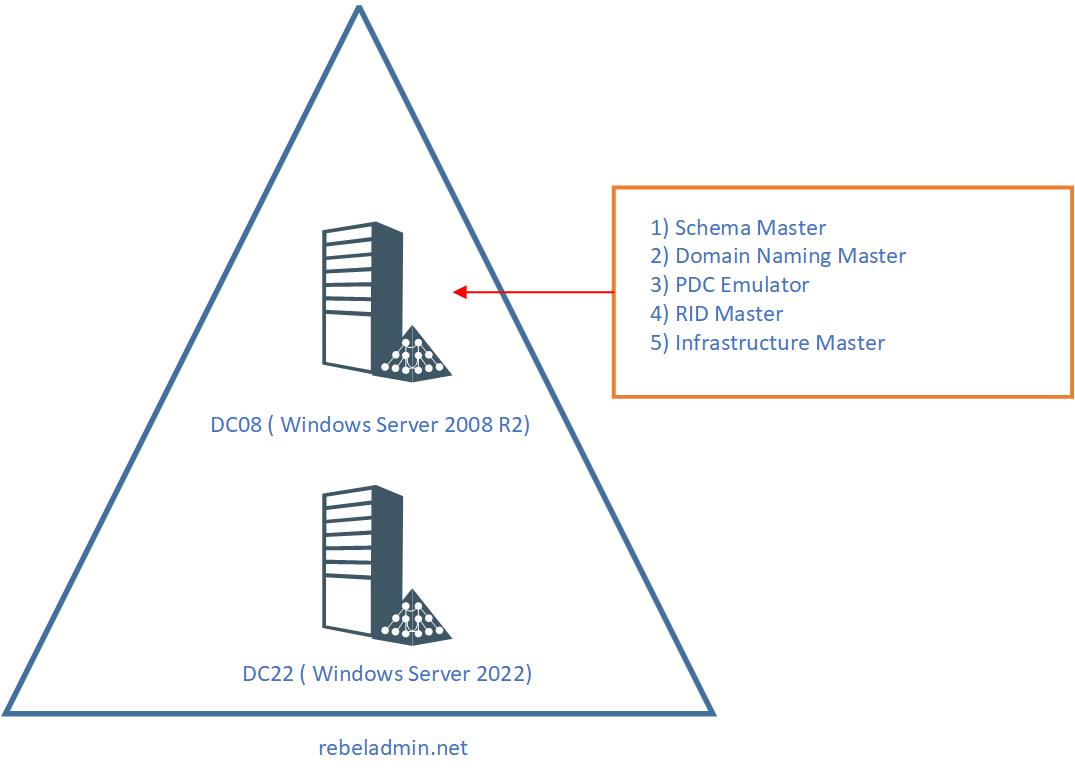
As per the following diagram, the rebeladmin.net domain has two domain controllers:
As explained in the above illustration, The FSMO role holder DC08 is a Windows Server 2008 R2 Domain Controller. The domain and forest functional levels currently operate in Windows Server 2008 R2. A new domain controller with Windows Server 2022(DC22) will be introduced and will be the new FSMO role holder for the domain. Once the FSMO role migration is complete, the domain controller running Windows Server 2008 R2 will be decommissioned. After that, the forest and domain functional levels will be raised to Windows Server 2016.
When you introduce new domain controllers to existing infrastructure, it is recommended that you introduce the forest root level first and then go to the domain tree levels.
Prepare Windows Server 2022 Domain Controller
We need to do few things to prepare the new Windows Server 2022 before we migrate the FSMO roles.
1. After the OS installation and Patching process is completed, go ahead and join the new Windows Server 2022 to the existing domain.
2. In Windows Server 2022, it is recommended to use PowerShell 7 instead of native Windows PowerShell. Please go to https://aka.ms/PSWindows for more information. At the time this article was written, the latest version was 7.1.4.
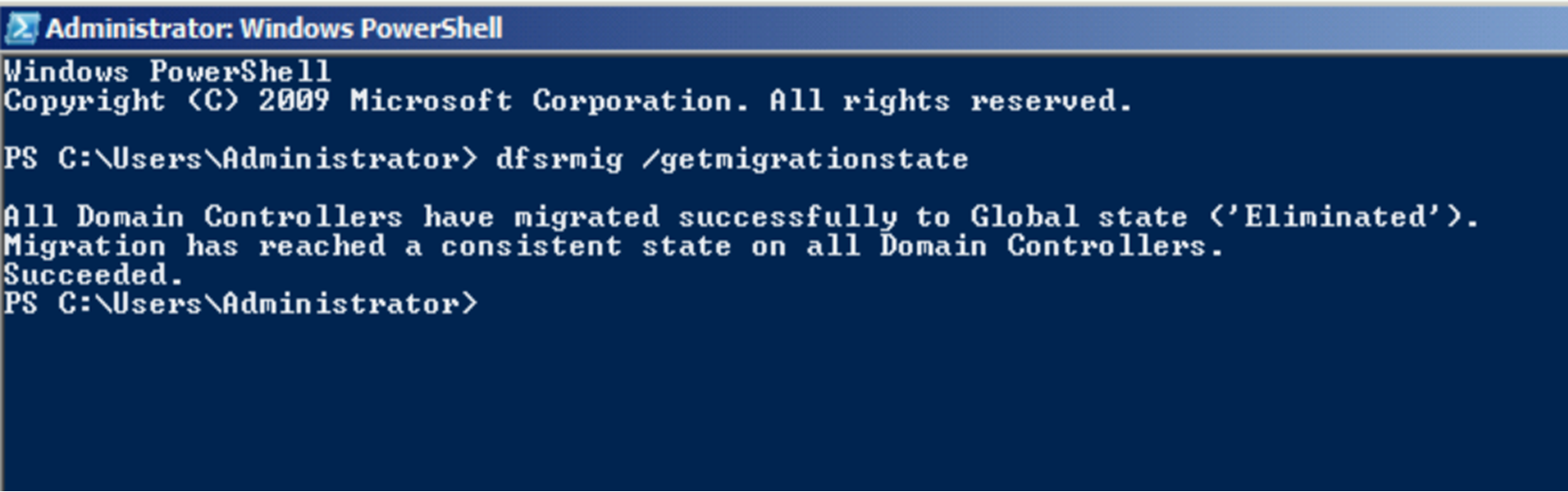
3. In the previous section, I mentioned before migration we need to make sure SYSVOL is using DFSR instead of FRS. To verify that, Log in to the DC08 domain controller (Windows Server 2008 R2) as a Domain Admin. Then run dfsrmig /getmigrationstate command in Powershell. If the command returns state as “eliminated“, it means DFSR is already in use for SYSVOL replication. If it is not, we must migrate SYSVOL replication to DFSR as Windows Server 2022 does not support FRS replication. FRS to DFSR migration steps are covered in a blog post I have written and it can access via https://www.rebeladmin.com/2015/04/step-by-step-guide-for-upgrading-sysvol-replication-to-dfsr-distributed-file-system-replication/
In this demo environment, the Domain controller already using DFSR.
Add Windows server 2022 Domain Controller
As the next part of the configuration, we need to make DC22 an Additional Domain Controller. To do that,
1. Log in to the server as an enterprise administrator.
2. Verify the static IP address allocation using ipconfig /all.
3. Launch the PowerShell 7 Console as an Administrator.
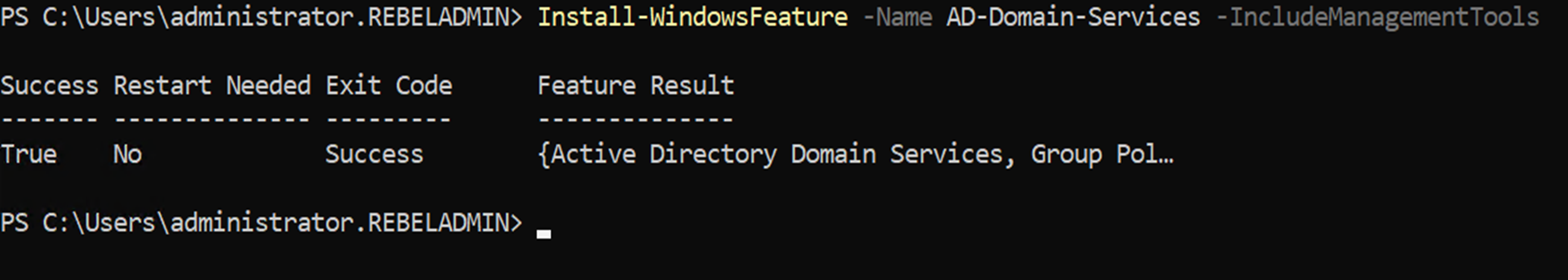
4. Before the configuration process, we need to install the AD DS Role in the given server. To do that we can use the following command.
Install-WindowsFeature -Name AD-Domain-Services -IncludeManagementTools
5. Configure the new server as an additional domain controller using,
Install-ADDSDomainController
-CreateDnsDelegation:$false
-InstallDns:$true
-DomainName “rebeladmin.net”
-SiteName “Default-First-Site-Name”
-ReplicationSourceDC “DC08.rebeladmin.net”
-DatabasePath “C:\Windows\NTDS”
-LogPath “C:\Windows\NTDS”
-SysvolPath “C:\Windows\SYSVOL”
-Force:$true
There are no line breaks for the command and I have listed it as above to allow readers to focus on the parameters.
The following table explains the PowerShell arguments and what it will do.
| Argument | Description |
| Install-ADDSDomainController | This cmdlet will install the domain controller in active directory infrastructure. |
| -CreateDnsDelegation | Using this parameter can define whether to create DNS delegation that reference active directory integrated DNS. |
| -InstallDns | Using this can specify whether DNS role need to install with active directory domain controller. For new forest, it is default requirement to set it to $true. |
| -DomainName | This parameter defines the FQDN for the active directory domain. |
| -SiteName | This Parameter can use to define the active directory site name. the default value is Default-First-Site-Name |
| -ReplicationSourceDC | Using this parameter can define the active directory replication source. By default, it will use any available domain controller. But if need we can be specific. |
| -DatabasePath | This parameter will use to define the folder path to store active directory database file (Ntds.dit) |
| -LogPath | Log path can use to specify the location to save domain log files. |
| -SysvolPath | This is to define the SYSVOL folder path. Default location for it will be C:\Windows |
| -Force | This parameter will force command to execute by ignoring the warning. It is typical for the system to pass the warning about best practices and recommendations. |
Once execute the command it will ask for SafeModeAdministrator Password. Please use a complex password to proceed. This will be used for DSRM.
FSMO Role Migration
Now we have the new domain controller. The next step is to migrate FSMO roles from DC08 to the new domain controller.
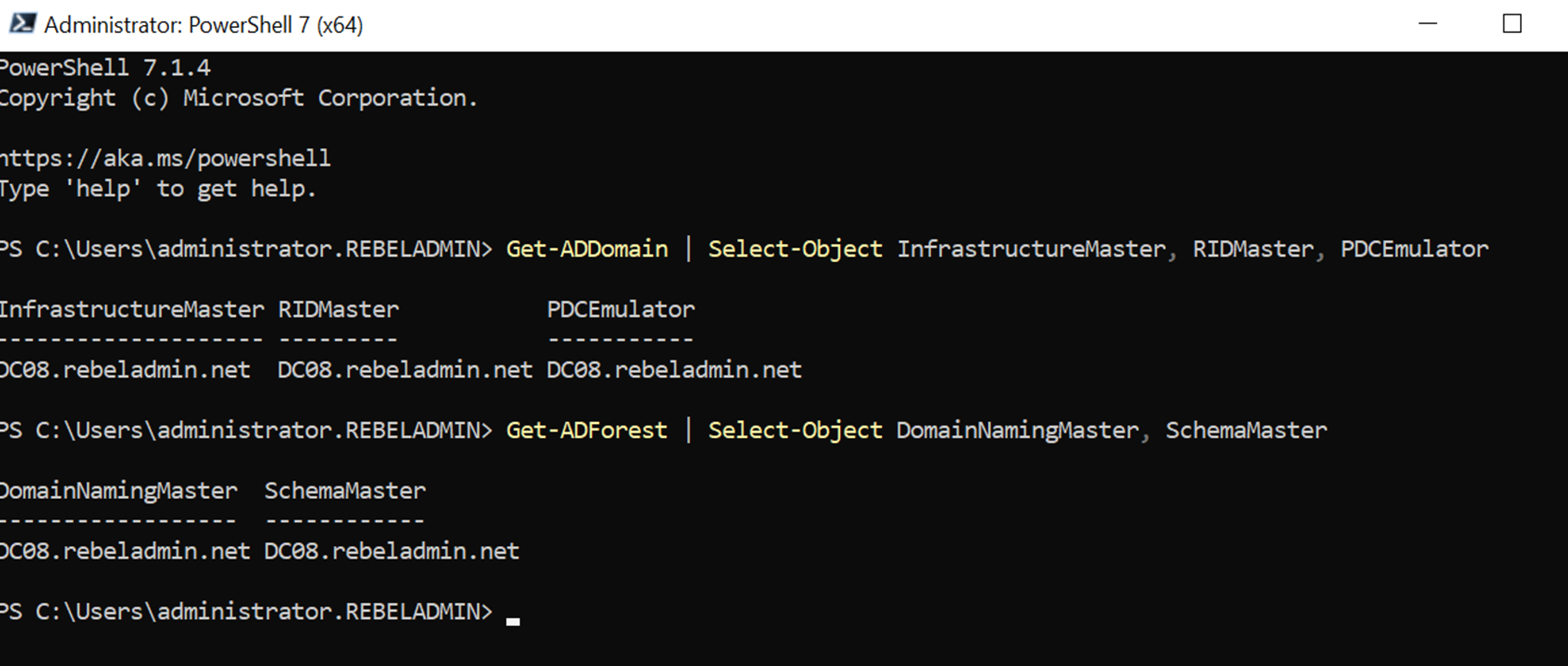
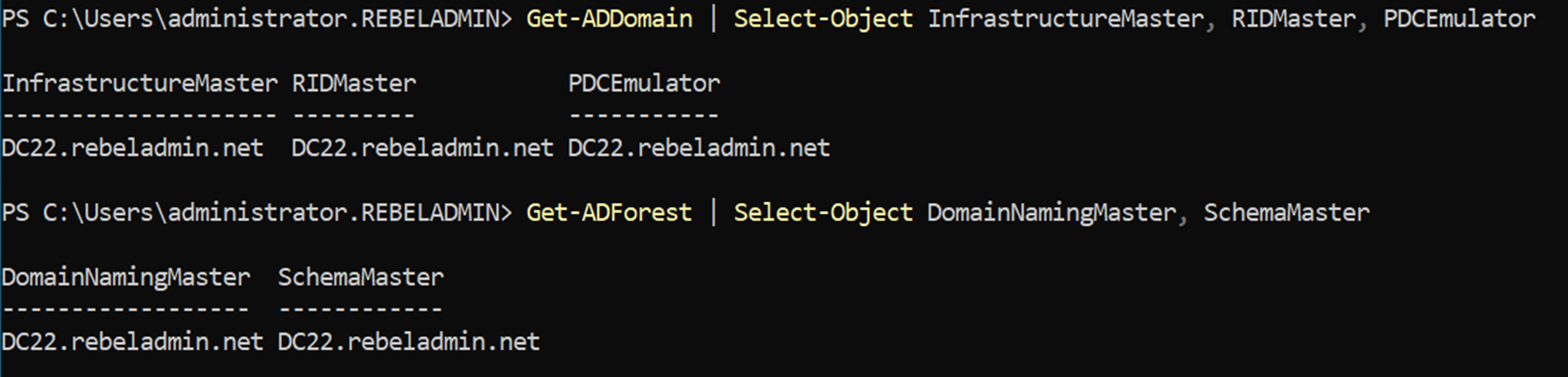
1. After the server is rebooted, log back in as an administrator. and run the following commands to verify the current FSMO role holder.
Get-ADDomain | Select-Object InfrastructureMaster, RIDMaster, PDCEmulator
Get-ADForest | Select-Object DomainNamingMaster, SchemaMaster
As we can see all five FSMO roles currently belong to DC08 (Windows Server 2008 R2) Domain Controller.
2. Migrate all five FSMO roles to the new domain controller by running the following command in DC02 server:
Move-ADDirectoryServerOperationMasterRole -Identity DC22 -OperationMasterRole SchemaMaster, DomainNamingMaster, PDCEmulator, RIDMaster, InfrastructureMaster
In the preceding command, DC22 is the domain controller running Windows Server 2022.
3. Once we’re done, we can verify the new FSMO role holder using the following command:
Get-ADDomain | Select-Object InfrastructureMaster, RIDMaster, PDCEmulator
Get-ADForest | Select-Object DomainNamingMaster, SchemaMaster
As expected, Now FSMO roles are successfully moved to DC22 Domain Controller (Windows Server 2022)
Decommission Old Domain Controller
Before we upgrade forest and domain functional levels, first we need to decommission the old DC which is running with windows server 2008 R2.
To do that,
1. Log in to old DC as enterprise administrator
2. Go to Run | dcpromo
3. It will open up the dcpromo wizard. Click on Next to continue.
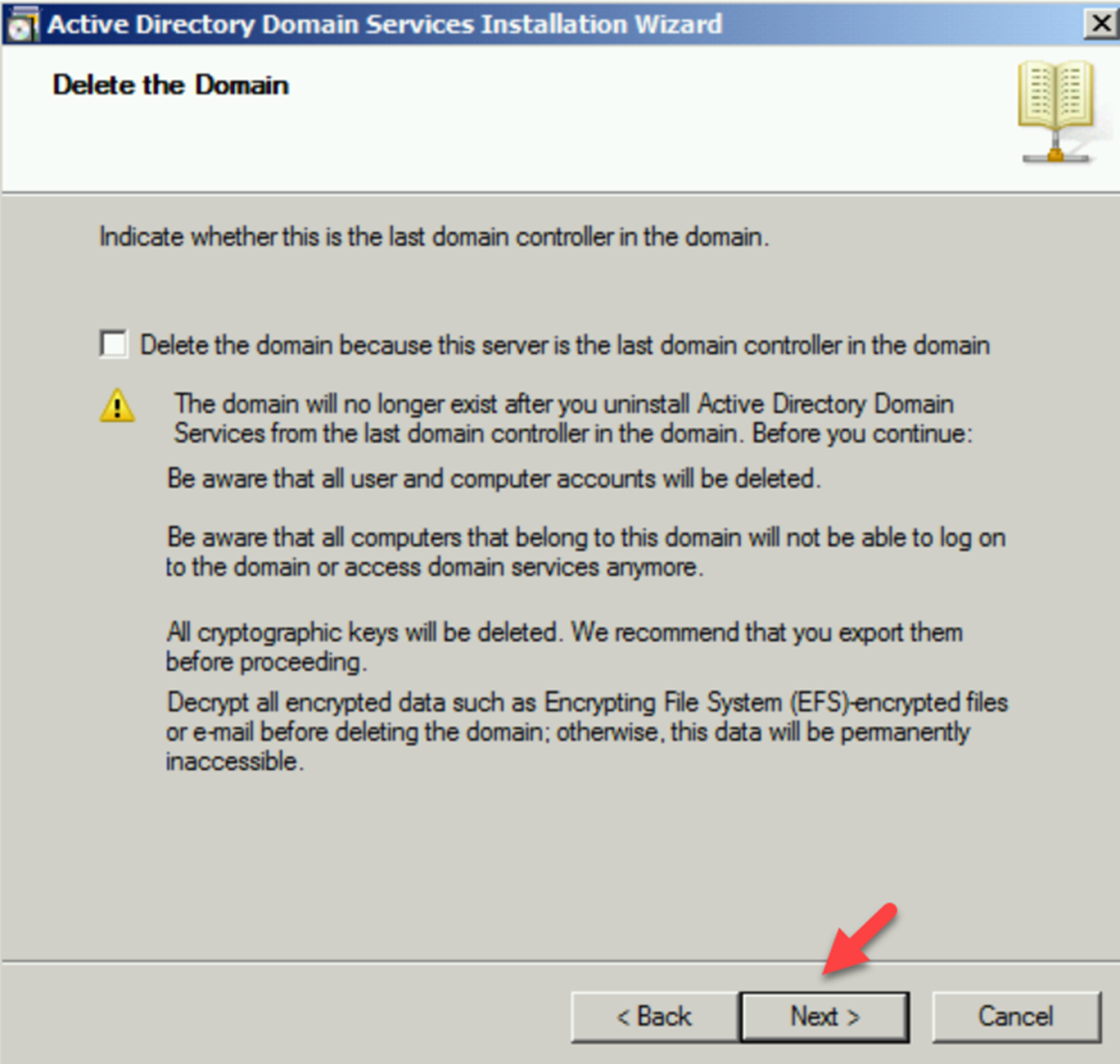
4. On the next page also click on Next as it is not the last domain controller.
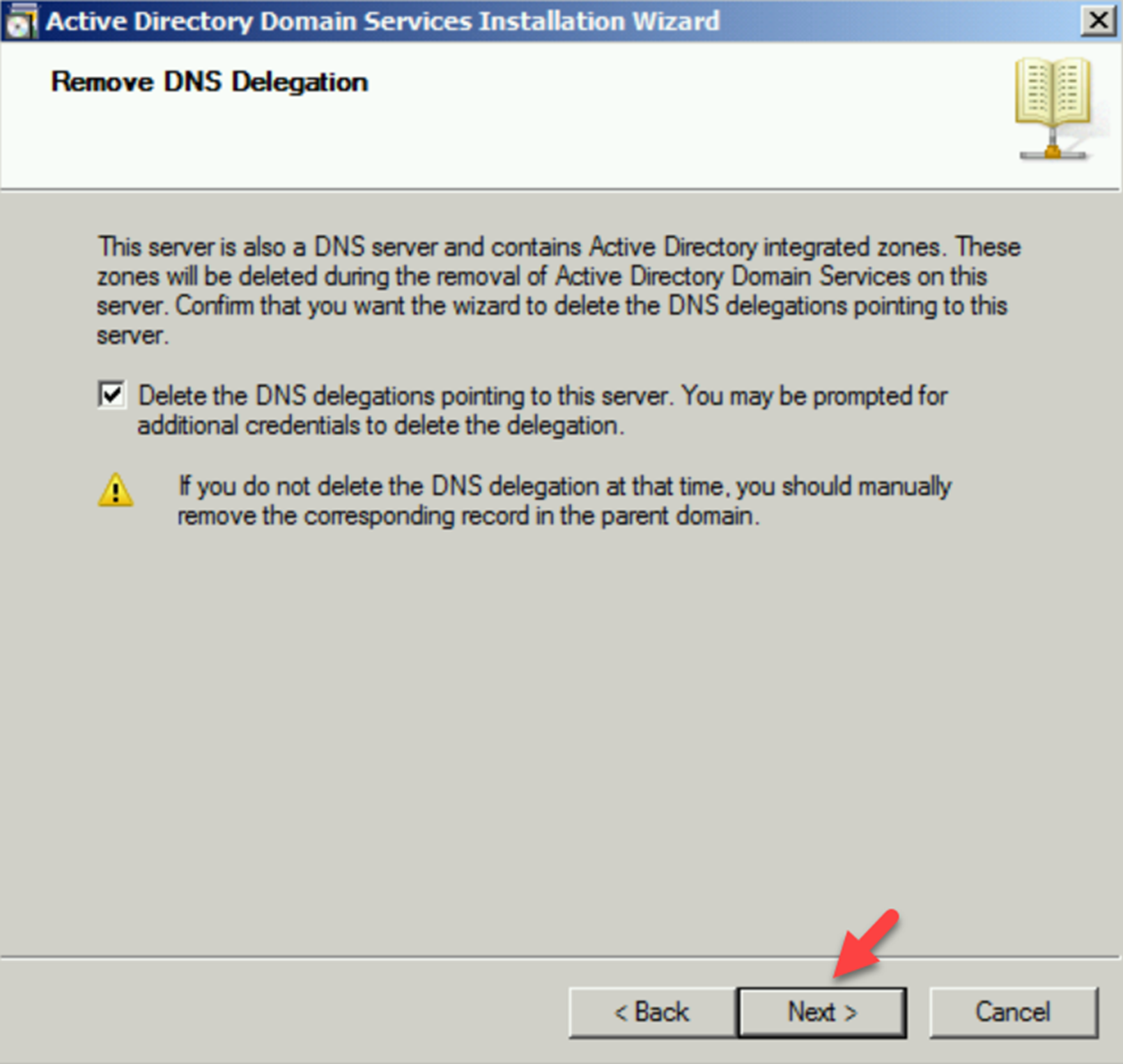
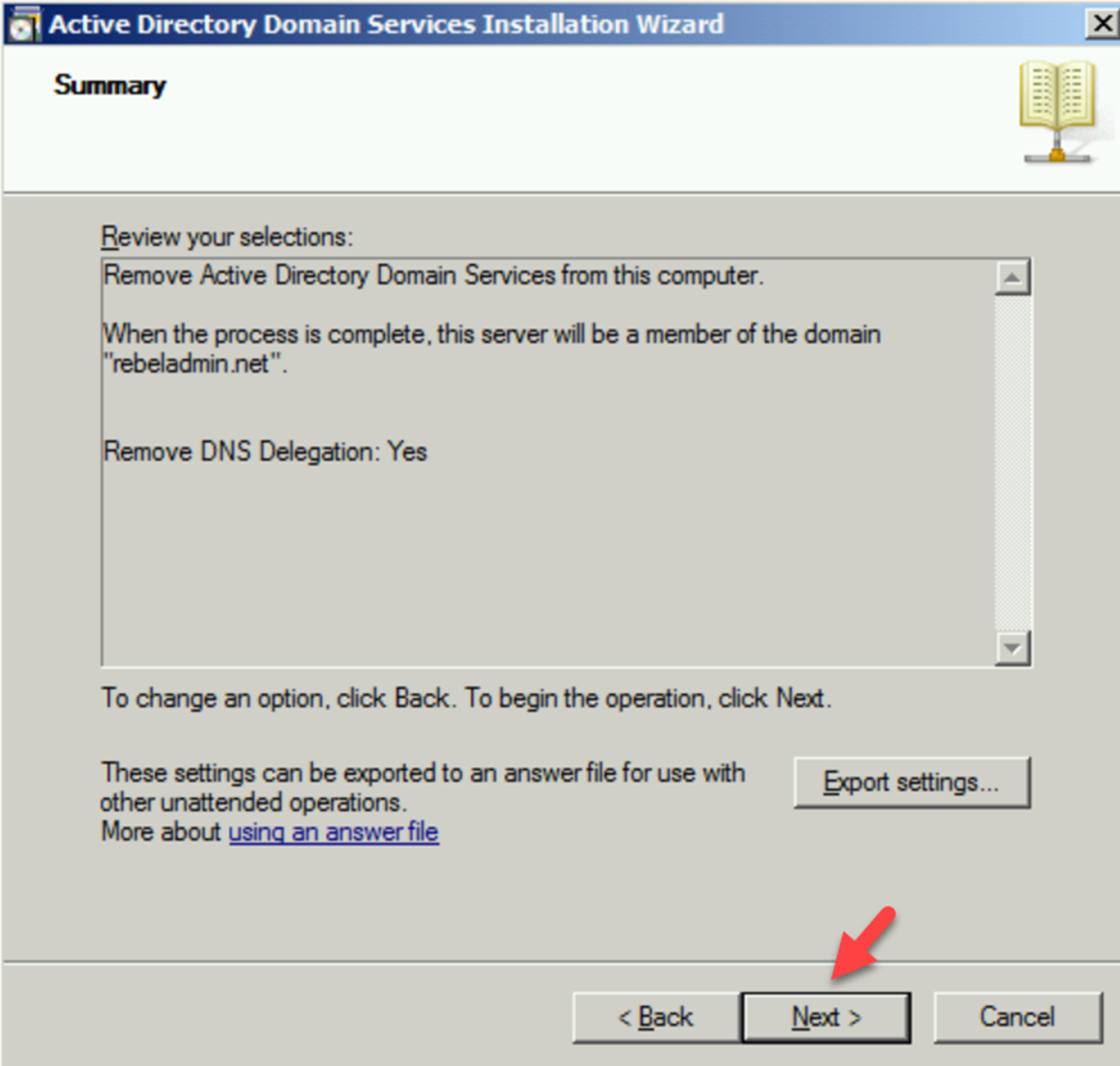
5. In the Remove DNS Delegation page keep the default selection and click on Next.
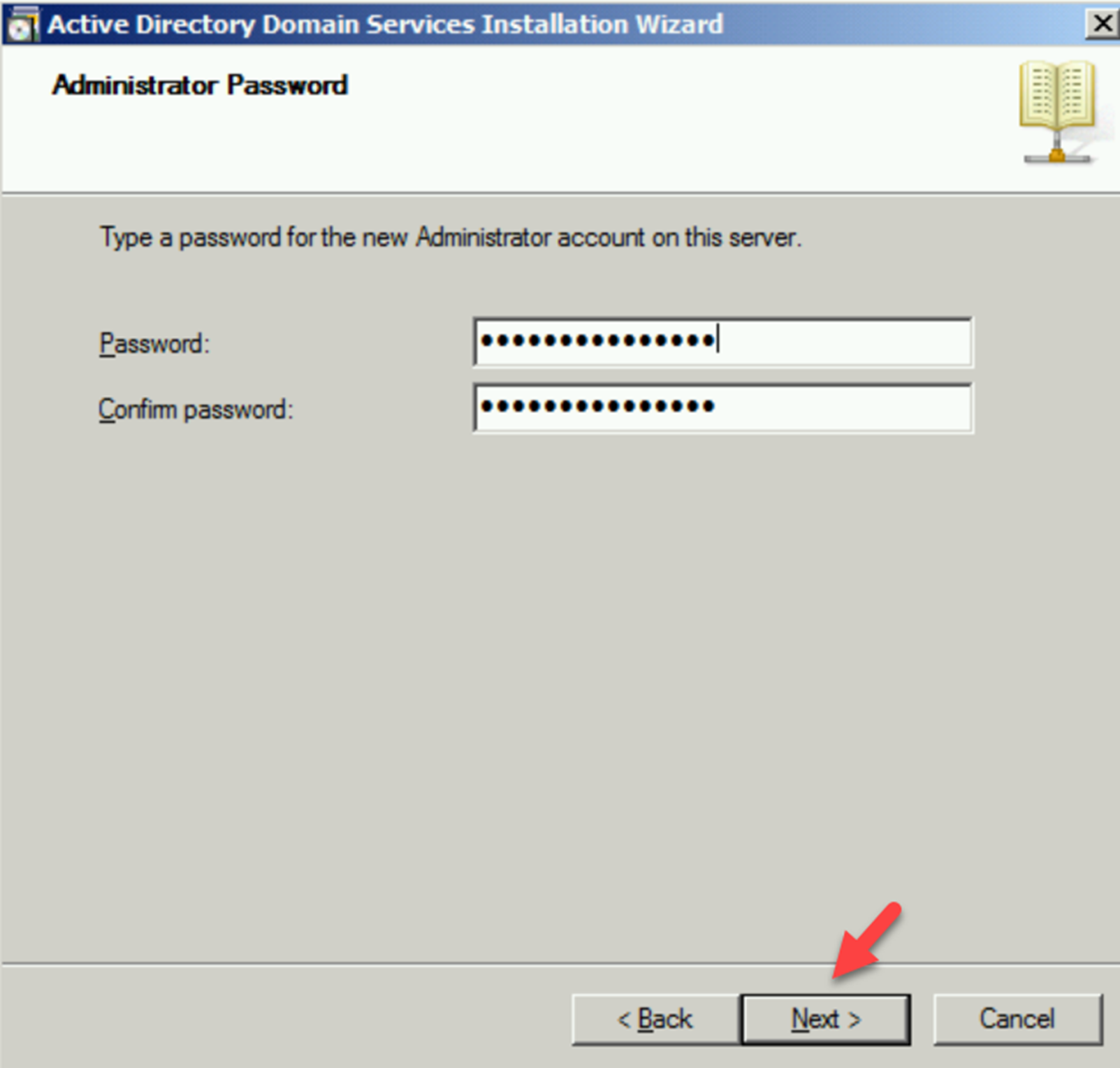
6. Then the system will prompt for credentials. Provide Domain Admin credentials here. On the next page, type a new password for the local administrator account.
7. In summary, page, click on Next to complete the process.
8. Once the process is completed, reboot the server.
If its Windows Server 2012 or above we can use Uninstall-ADDSDomainController -DemoteOperationMasterRole -RemoveApplicationPartition to uninstall AD DS
Raise Domain and Forest Functional level
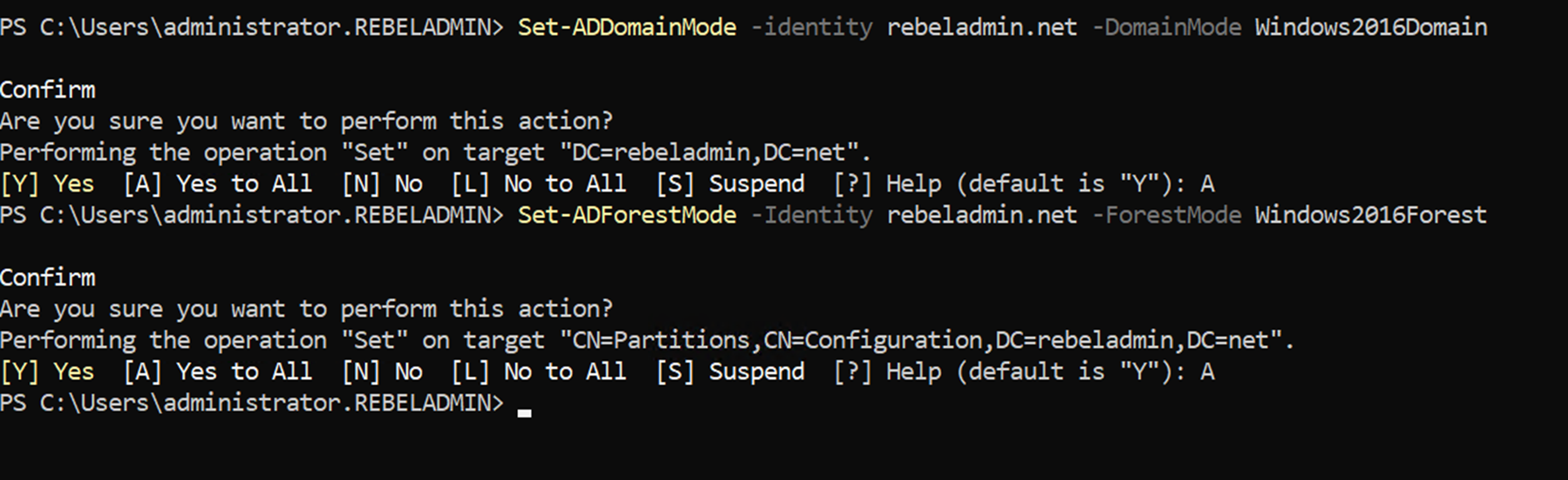
After you demote your last domain controller running with windows server 2008 R2, we can raise Domain and Forest Functional level to windows server 2016 (Windows server 2022 is the same).
To upgrade the domain functional level, we can use the following PowerShell command in the Windows server 2022 domain controller.
Set-ADDomainMode -identity rebeladmin.net -DomainMode Windows2016Domain
To upgrade forest functional level, use the following command:
Set-ADForestMode -Identity rebeladmin.net -ForestMode Windows2016Forest
Now, we have completed the migration from AD DS 2008 R2 to AD DS 2022. The same steps apply when you’re migrating from Windows Server 2012, Windows Server 2012 R2, Windows Server 2016, and Windows Server 2019.
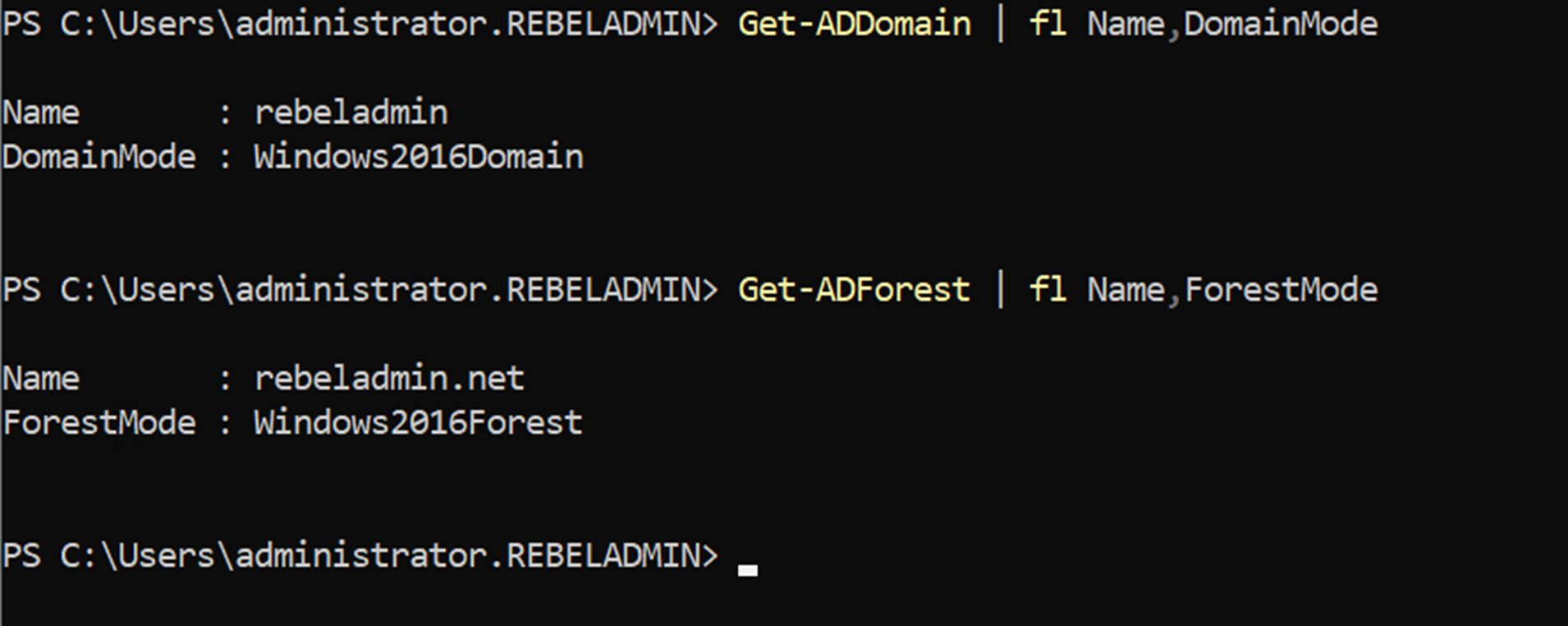
Verification
Although the migration is complete, we still need to verify whether it’s completed successfully. The following command will show the current domain functional level of the domain after the migration:
Get-ADDomain | fl Name,DomainMode
The following command will show the current forest functional level of the domain after migration:
Get-ADForest | fl Name,ForestMode
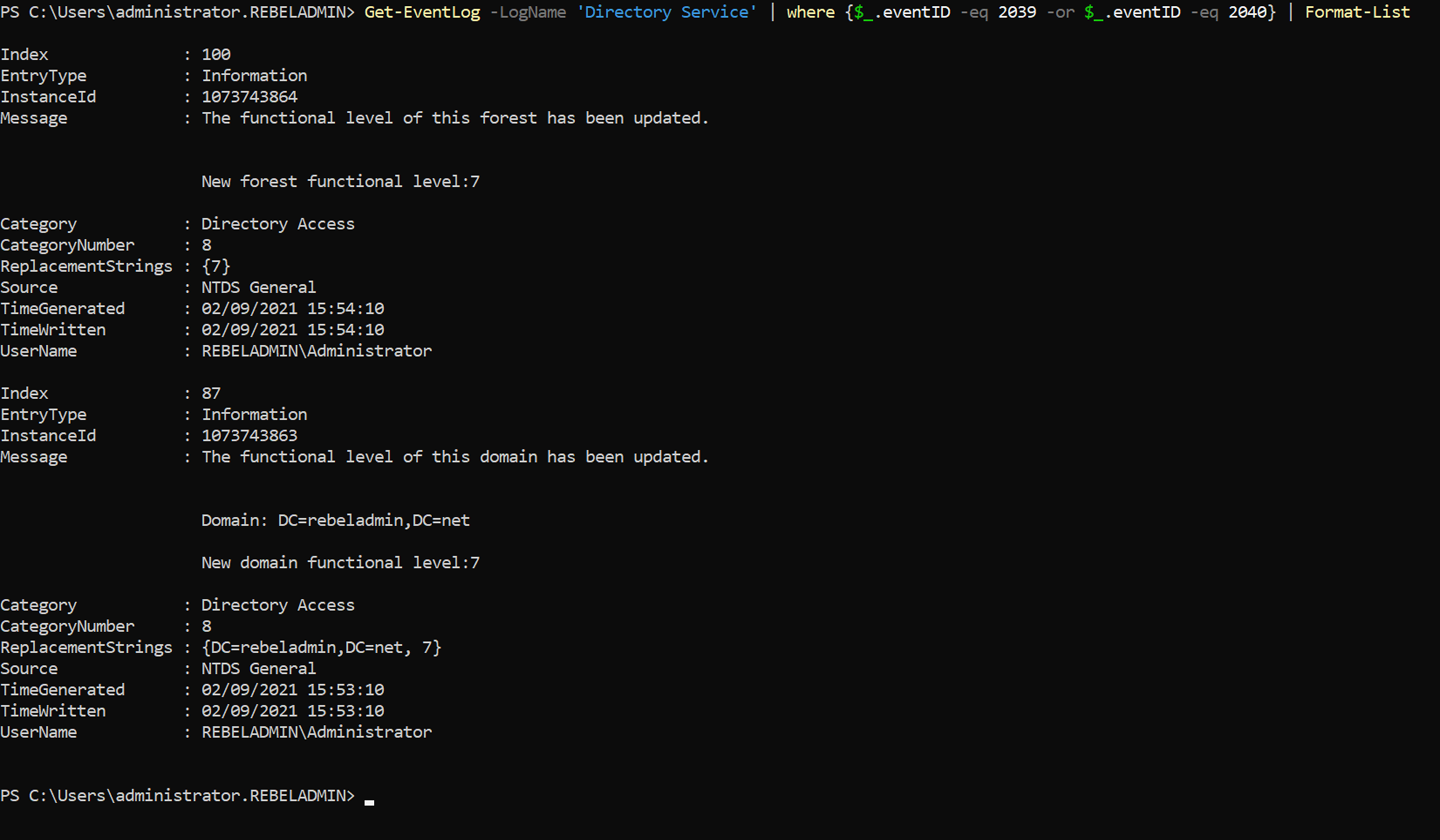
You can also use the following command to verify the forest & domain functional level updates:
Get-EventLog -LogName ‘Directory Service’ | where {$_.eventID -eq 2039 -or $_.eventID -eq 2040} | Format-List
The following screenshot shows events 2039 and 2040 in the Directory Service log, which verify the forest and domain functional level updates:
Event ID 1458 verifies the transfer of the FSMO roles:
Get-EventLog -LogName ‘Directory Service’ | where {$_.eventID -eq 1458} | Format-List
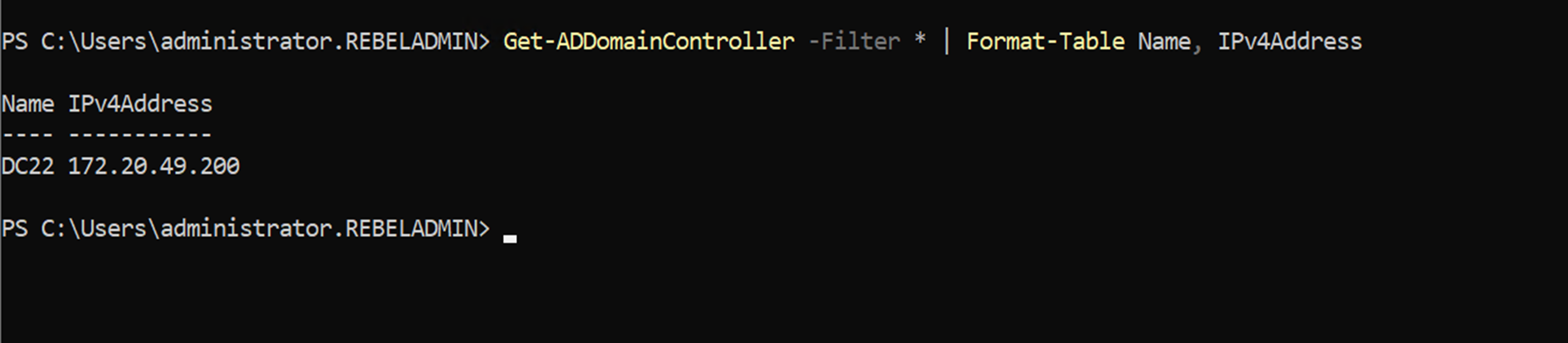
We can use the following command to verify the list of domain controllers and make sure that the old domain controller is gone:
Get-ADDomainController -Filter * | Format-Table Name, IPv4Address
This marks the end of this blog post. If you have any questions feel free to contact me at rebeladm@live.com. Also, follow me on Twitter @rebeladm to get updates about new blog posts.




Great write up. Thank you very much Dishan.
Do we need to give some more time for upgrading to 2022 as it only like few weeks or days the OS has been released?
You’d be the first site I’ve seen who mentions you can skip domain/forest functional levels. This was hard to google, since I didn’t know if you had to step up the levels 2008R2 – 2012 – 2012R2 – 2016. Appreciate your contribution and detail.
Thanks for this. Helped me a lot with my small project.
nice article. thank you.
Thank you very much for this write-up! Extremely helpful!