Last Updated on January 1, 2018 by Dishan M. Francis
This is my first blog post in 2018. So, first of all Happy New year to my blog readers!
In many occasions, I have written articles about Active Directory Migrations. But still I get lots of emails from readers to clarify things about AD migrations. So, I thought to revisit it by covering most common questions I gets. Also in this blog post, I will show how to do the AD migration only using PowerShell.
Migration task itself is very straight forward. But there are other things you need to consider before you do an AD migration. In below I listed a checklist you can use in many occasions.
Active Directory Migration Check List
Evaluate business requirement for active directory migration
Perform Audit on Existing Active Directory Infrastructure to verify its health status
Create Plan for implementation Process
Prepare Physical / Virtual resources for Domain Controller
Install Windows server 2016 Standard / Datacenter
Patch Servers with latest Windows Updates
Assign Dedicate IP address to Domain Controller
Install AD DS Role
Migrate Application and Server Roles from the Existing Domain Controllers
Migrate FSMO roles to new Domain Controllers
Add New Domain controller to the Existing DR Solution
Decommission old domain controllers
Raise the Domain and Forest Functional level
On Going Maintenance
Tips – During audit process you need to verify if your applications will support new AD schema. it is very rare but I have seen legacy applications which is not support newer schema versions.
Also in some scenarios, it is hard to replace primary dc with a DC running with different IP address. AD is supported for IP changes even after FSMO role changes. There for if need you can swap IP addresses after you migrate FSMO roles.
Topology
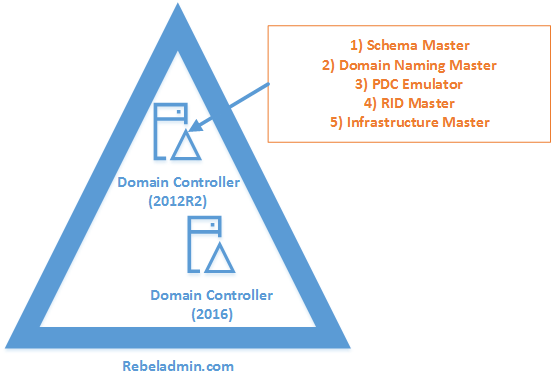
In my demo environment, I have an existing domain controller running with windows server 2012 R2. I am going to migrate it to a windows server 2016 server.
In the demonstration, REBEL-WIN-DC01 is the domain controller with windows server 2012 R2 and REBEL-SDC01 is the domain controller with windows server 2016.
Tip – When you introduce new domain controllers to the existing infrastructure it is recommended to introduce to the forest root level first and then go to the domain tree levels.
Add Additional Domain Control
As per plan I need to add a new domain controller with windows server 2016 to existing domain first.
1) Log in to the Server (Windows server 2016) as a member of local administrators group.
2) Add server to the existing domain as member.
3) Log in to domain controller as enterprise administrator.
4) Verify the static IP address allocation using ipconfig /all.
5) Launch the PowerShell Console as an Administrator
6) Before the configuration process, we need to install the AD DS Role in the given server. In order to do that we can use Following command.
Install-WindowsFeature –Name AD-Domain-Services -IncludeManagementTools
7) After successful role service Installation, next step is to configure the domain controller. It can be done using following PowerShell command.
Install-ADDSDomainController
-CreateDnsDelegation:$false
-InstallDns:$true
-DomainName "rebeladmin.com"
-SiteName "Default-First-Site-Name"
-ReplicationSourceDC "REBEL-WIN-DC01.rebeladmin.com"
-DatabasePath "C:\Windows\NTDS"
-LogPath "C:\Windows\NTDS"
-SysvolPath "C:\Windows\SYSVOL"
-Force:$true
|
Argument
|
Description
|
|
Install-ADDSDomainController
|
This cmdlet will install the domain controller in active directory infrastructure.
|
|
-SiteName
|
This Parameter can use to define the active directory site name. the default value is Default-First-Site-Name
|
|
-DomainName
|
This parameter defines the FQDN for the active directory domain.
|
|
-ReplicationSourceDC
|
Using this parameter can define the active directory replication source. By default, it will use any available domain controller. But if need we can be specific.
|
|
-InstallDns
|
Using this can specify whether DNS role need to install with active directory domain controller. For new forest, it is default requirement to set it to $true.
|
|
-LogPath
|
Log path can use to specify the location to save domain log files.
|
|
-SysvolPath
|
This is to define the SYSVOL folder path. Default location for it will be C:\Windows
|
|
-Force
|
This parameter will force command to execute by ignoring the warning. It is typical for the system to pass the warning about best practices and recommendations.
|
Once execute the command it will ask for SafeModeAdministrator Password. Please use complex password to proceed. This will be used for DSRM.
After configuration completed, restart the system and log back in as administrator to check the AD DS status.
Get-Service adws,kdc,netlogon,dns
Move FSMO Roles
Now we have additional domain controller and next step is to migrate FSMO roles to the new server.
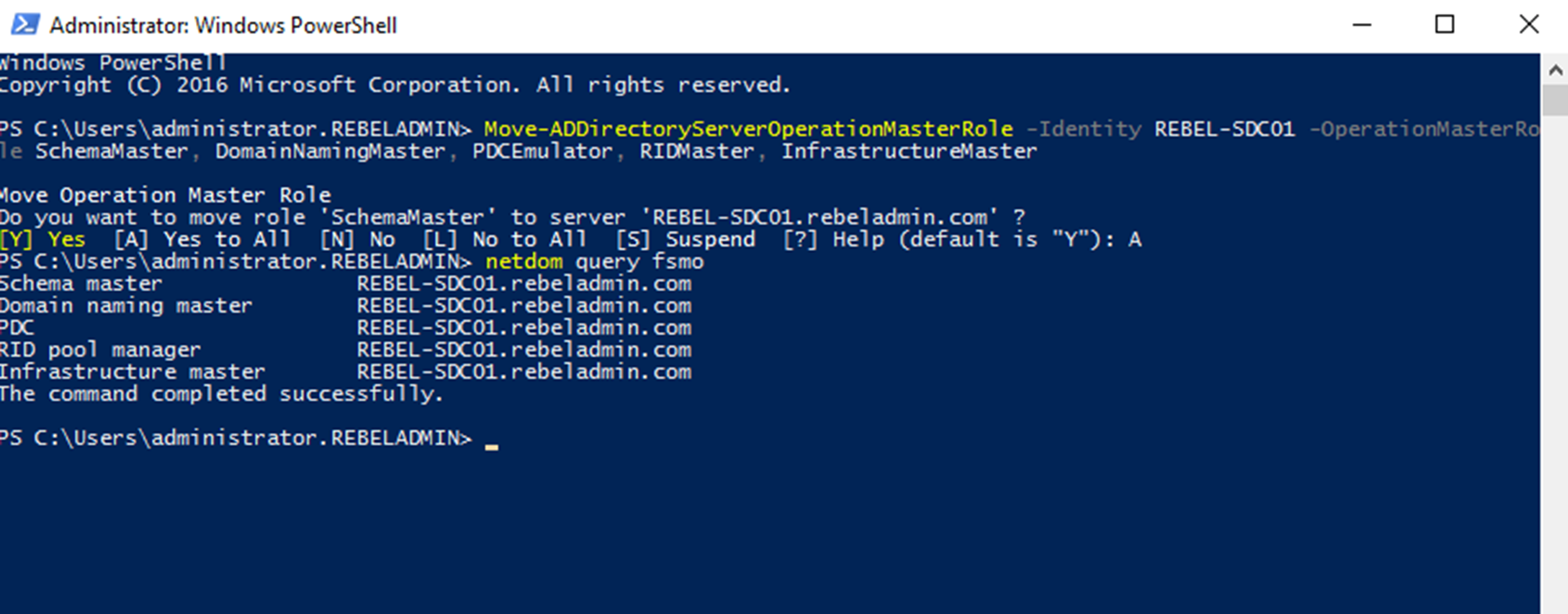
We can migrate all five FSMO roles to the New domain controller using following powershell command,
Move-ADDirectoryServerOperationMasterRole -Identity REBEL-SDC01 -OperationMasterRole SchemaMaster, DomainNamingMaster, PDCEmulator, RIDMaster, InfrastructureMaster
In above the REBEL-SDC01 is domain controller running with windows server 2016. Once its completed, we can verify the new FSMO role holder using
Netdom query fsmo
Decommission Old Domain Controller
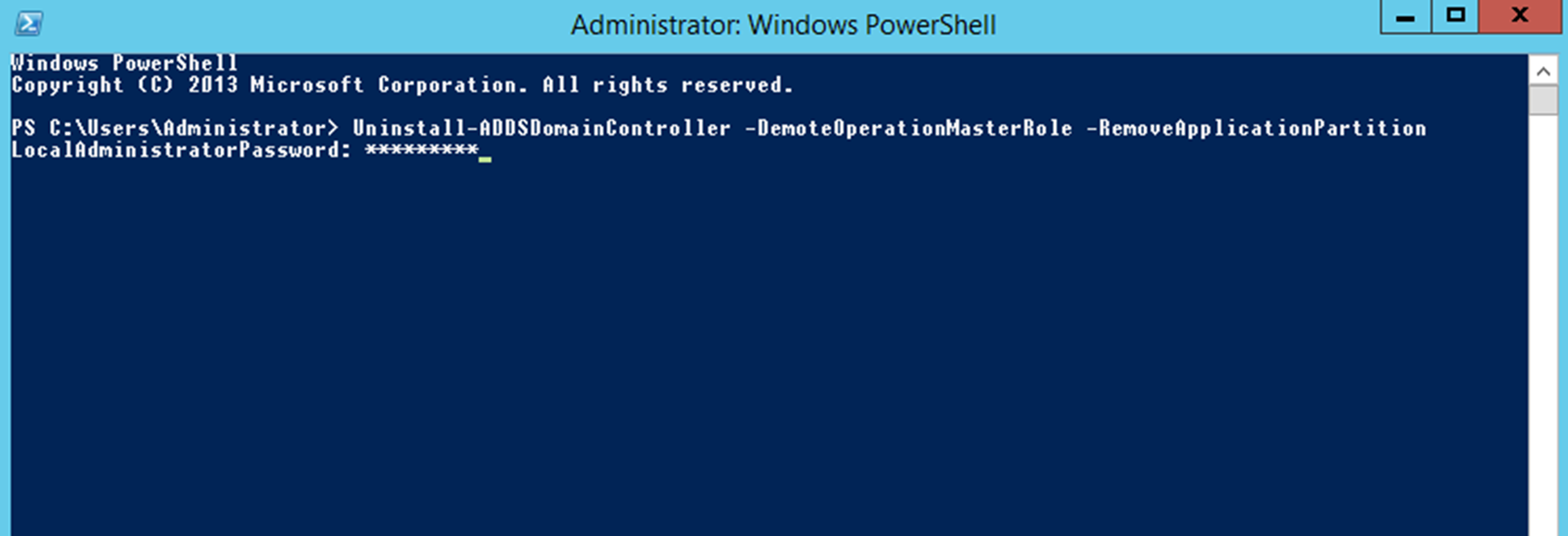
Now we moved FSMO roles over and next step is to decommission old DC which is running with windows server 2012 R2.
In order to do that, log in to old DC as enterprise administrator and run following powershell command,
Uninstall-ADDSDomainController -DemoteOperationMasterRole -RemoveApplicationPartition
After execute the command it will ask to define password for the local administrator account.
Once its completed it will be a member server of the rebeladmin.com domain.
Raise Domain and Forest Functional level
After you remove your last domain controller running with windows server 2012 r2 (if its 2012 or 2008 r2 same thing apply) we can raise Domain and Forest Functional level to windows server 2016. You need it to have features comes with AD 2016.
To upgrade domain functional level, you can use following powershell command
Set-ADDomainMode –identity rebeladmin.com -DomainMode Windows2016Domain
To upgrade forest function level, you can use following command
Set-ADForestMode -Identity rebeladmin.com -ForestMode Windows2016Forest
After the migration completes we still need to verify if its completes successfully.
Get-ADDomain | fl Name,DomainMode
This command will show the current Domain functional level of the domain after the migration.
Get-ADForest | fl Name,ForestMode
Above command will show the current forest functional level of the domain.
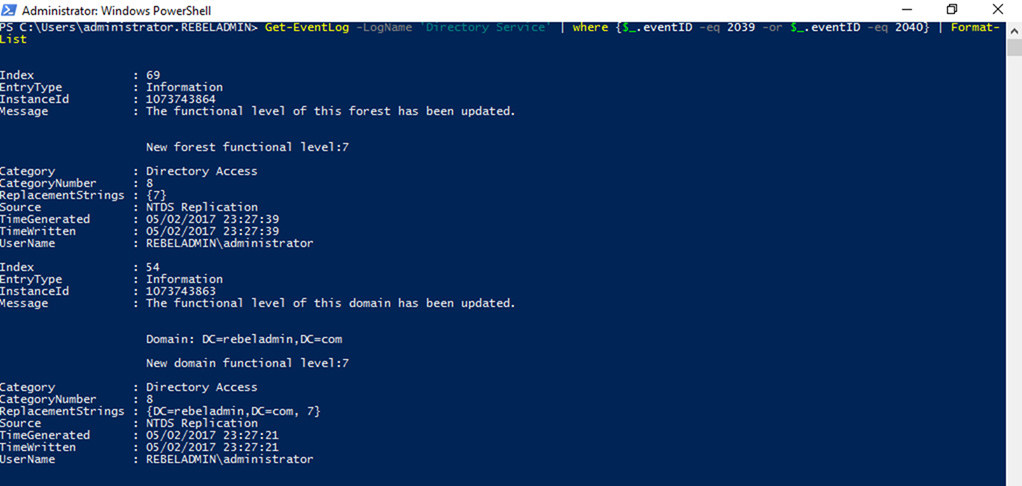
Also, you can use
Get-EventLog -LogName 'Directory Service' | where {$_.eventID -eq 2039 -or $_.eventID -eq 2040} | Format-List
To search event ID 2039 and 2040 in the “Directory Service” log which will show the forest and domain functional level updates.
Event ID 1458 will verify the transfer of the FSMO roles.
Get-EventLog -LogName 'Directory Service' | where {$_.eventID -eq 1458} | Format-List
You can use following to verify the list of domain controllers and make sure the old domain controller is gone.
Get-ADDomainController -Filter * | Format-Table Name, IPv4Address
Apart from these you also can go through Directory Service and DNS Logs to see if there’s any issues recorded.
This marks the end of this blog post. Hope this was useful. If you have any questions feel free to contact me on
rebeladm@live.com also follow me on twitter
@rebeladm to get updates about new blog posts.



Hi
thanks for this Great explanation.can you also mention something About moving DHCP from old to new server?